Article 3 – Information Technology
5.3.1 Lost and Stolen IT Assets
-
Policy
-
California Correctional Health Care Services (CCHCS) staff shall submit an Information Security Incident Report (ISIR) via a Solution Center ticket, to Local Information Technology (IT) staff within three days of identifying a lost or stolen IT asset.
-
-
Applicability
-
This policy applies to all CCHCS staff, contracted personnel, volunteers, and vendors utilizing IT assets.
-
-
Procedure
-
Attempting to Locate Lost IT Assets
-
Staff shall search the surrounding area where the IT asset was last assigned/seen.
-
Staff shall inform their supervisor or manager that the IT asset is missing to determine if others may be aware of the asset being moved to another location. If still unable to locate the IT asset after notifying supervisor or manager, staff shall follow the process as outlined in Section (c)(3), Reporting Lost or Stolen IT Assets.
-
-
Determining IT Asset Disposition
-
Local IT shall:
-
Determine the IT asset disposition by checking all applicable databases and network activity of the IT asset, per the Information Technology Services Division (ITSD) Lost and Stolen IT Assets Procedure.
-
Widen the search of the surrounding area (arrange with California Department of Corrections and Rehabilitation/CCHCS Program Supervisors):
-
Notify the Chief Executive Officer or CCHCS site leadership to perform site-wide CCHCS physical inventory (local IT staff will provide asset information to site leadership and inform them of all activities performed to locate missing asset).
-
If the IT asset is lost/stolen at an institution:
-
Notify the Watch Commander, Investigative Services Unit, and Warden of the missing IT asset
-
Provide the asset tag number and model.
-
CCHCS Local IT staff shall assist program staff with physical inventory of equipment, if needed.
-
-
-
-
Reporting Lost or Stolen IT Assets
-
Staff shall obtain a local law enforcement report to complete required notifications for stolen IT assets.
-
In the event an IT asset is stolen on state property, the local law enforcement agency is the California Highway Patrol (CHP). The Department of General Services STD. 99, Report of Crime or Criminally Caused Property Damage on State Property, form is required in the event CHP is involved.
-
-
Staff shall notify local IT immediately via a Solution Center ticket when an IT asset is determined lost/stolen. Local IT shall assist, as necessary, in documenting the following information within the ticket:
-
If IT Asset is determined stolen:
-
Name of the local law enforcement department reported to.
-
Report number.
-
If crime occurred on state property, complete the STD. 99 and notify the nearest CHP office. Return the completed STD. 99 form to the Information Security Office (ISO).
-
-
Phone number of the device (if applicable).
-
Model of the device.
-
Serial number of the device.
-
Asset tag number of the device.
-
Last location of the IT asset.
-
Did it contain sensitive, confidential, or Protected Health Information?
-
If capable, was the IT asset password/PIN protected?
-
Include the ISO on the Solution Center ticket. The ISO shall add pertinent information to the ticket.
-
-
Within three business days, and once determined appropriate to do so, Local IT shall direct staff to complete the CCHCS ISIR, located on the Information Security page of Lifeline under “Information Security Reporting Procedure, How to Report an Information Security Event”.
-
The completed ISIR shall be attached to the Solution Center ticket.
-
-
Local IT staff shall send notification containing the above information to appropriate parties, per the ITSD Lost and Stolen IT Assets Procedure.
-
For mobile phones, local IT shall attempt to locate the phone per the ITSD Lost and Stolen IT Assets Procedure.
-
If an IT asset was lost/stolen in an institution, the local hot trash custody processes shall be followed for any components that are missing.
-
-
Finding a Lost/Stolen IT Asset
-
If a lost/stolen IT asset is found, local IT shall:
-
Update and resolve the CCHCS Solution Center ticket.
-
Notify all parties involved.
-
Update the IT asset disposition in all applicable locations.
-
-
-
References
-
ITSD Lost and Stolen IT Assets Procedure
-
STD. 99 – Report of Crime or Criminally Caused Property Damage on State Property: https://www.documents.dgs.ca.gov/dgs/FMC/PDF/std099.pdf
-
STD. 152 Property Survey Sheet: https://www.documents.dgs.ca.gov/dgs/fmc/pdf/std152.pdf
-
STD. 158 Property Transfer Report: https://www.documents.dgs.ca.gov/dgs/fmc/pdf/std158.pdf
-
CCHCS Information Security Incident Report (ISIR): Information Technology – CCHCS Information Security Incident Form.pdf – All Documents (sharepoint.com)
-
Locating a CHP Office: https://www.chp.ca.gov/find-an-office
-
-
Revision History
-
Effective: 01/2022
-
5.3.2 Camera Use
-
Policy
-
California Correctional Health Care Services (CCHCS) staff shall ensure all CCHCS cameras, camera-enabled devices, and video monitoring equipment on state grounds are for health care purposes only including, but not limited to, taking photographs or conducting Telemedicine, Telepsychiatry, or Telepsychology encounters.
-
-
Purpose
-
To safeguard confidential information and reduce opportunities for harassment, unauthorized disclosure and distribution, CCHCS regulates the use of electronic equipment used to capture or store images such as smart phones, video equipment, cameras, tablets, handheld scanners, and flash drives.
-
-
Responsibilities
-
The Hiring Authority, or designee, shall approve the use of state-issued cameras, camera-enabled devices, and video monitoring equipment in advance.
-
The CCHCS Deputy Director of Communications and Institution Public Information Officer shall be consulted for the added supervision or security arrangement when media’s use of cameras or video-enabled devices are to be accommodated.
-
The Information Technology Services Division is responsible for managing the procurement, architecture, data communication network, implementation, access control, ongoing hardware and software support contracts and licensing for the camera-enabled audio or video systems.
-
-
Procedure
-
Usage
-
CCHCS authorizes the use of cameras or video-enabled devices for:
-
Conducting state business;
-
Facilitating the delivery of health care related instruction;
-
Providing patients with access to care;
-
Monitoring and improving patient outcomes (e.g., wound care, Root Cause Analysis, Performance Improvement Work Plans).
-
-
Employees shall not use cameras or video-enabled devices to create or convey offensive, harassing, vulgar, obscene, or threatening images or communications. Similarly, transmitting sexually oriented messages, videos or images at work using camera-enabled devices is forbidden pursuant to Department Operations Manual (DOM), Section 31010.5, Conduct Violations; and Section 31010.6, Sexual Harassment Violations. Camera-enabled devices on CCHCS premises or at state-sponsored events shall not be used to defame, embarrass, or disparage the state, employees, patients, customers, or vendors, or be used to video record or photograph privileged or confidential material.
-
-
Guidelines
-
All CCHCS mobile devices (includes laptops and tablets) shall be issued with the camera enabled as the default setting.
-
Any photography or video recording within an institution, where patient images or videos may be captured, shall be handled pursuant to DOM Section 13010.17, Photographs, Films, and Videotapes.
-
Cameras or video-enabled devices with lens covers shall remain closed when the camera is not in use.
-
The staff working in clinical settings shall obtain written consent from the patient being photographed or video recorded.
-
The CDCR 7120, Informed Consent for Clinical Photography/Digital Imaging, shall be completed and scanned into the health record for each patient.
-
If the patient is unable to provide consent, staff shall document that on the CDCR 7225, Refusal of Examination and/or Treatment, for clinical documentation purposes.
-
-
Employees shall report any violations of this policy to their supervisor in writing. Any images or videos taken on CCHCS property using CCHCS equipment are considered state property. Any images or videos found in violation of this policy are subject to confiscation. Violation of this policy may result in discipline, up to and including termination of employment.
-
-
Unauthorized Disabling or Tampering
-
Unauthorized disabling of or tampering with installed cameras or video-enabled devices shall be cause for disciplinary action.
-
-
-
References
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 1, Article 13, Section 13010, Public/Media Information
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 1, Article 13, Section 13010.17, Photographs, Films, and Videotapes
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 2, Article 12, Section 22030.12.1, Sensitive Property
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 1, Section 31010.5, Conduct Violations
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 1, Section 31010.6, Sexual Harassment Violations
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Section 48010.5 – Acceptable Uses and Ethics
-
Health Care Department Operations Manual, Chapter 3, Article 1, Section 3.1.20 – Clinical Photography Digital Imaging
-
Health Care Department Operations Manual, Chapter 5, Article 3, Section 5.3.15, Acceptable Use
-
-
Revision History
-
Effective: 06/16/2023
-
5.3.3 CCHCS‑Issued Mobile Phone
-
Policy
-
California Correctional Health Care Services (CCHCS) shall maintain standards and requirements regarding approval, distribution, and acceptable use of CCHCS-issued mobile phones. CCHCS staff and contracted personnel that are issued a CCHCS mobile phone to conduct official state business shall abide by the procedure and guidelines stated herein.
-
-
Applicability
-
This policy applies to all CCHCS staff and contracted personnel.
-
-
Responsibilities
-
The hiring authority (HA), or designee, is responsible for approving requests to issue mobile phones and to ensure appropriate usage of the phone.
-
The Information Technology Services Division (ITSD) is responsible for issuing mobile phones.
-
The ITSD is responsible for managing the procurement, architecture, data communication network, access control, and ongoing hardware and software support contracts for the mobile phones.
-
-
Procedure
-
Requesting a New Mobile Phone
-
All requests for mobile phones shall be submitted through a Solution Center ticket:
-
By, or on behalf of, the Chief Executive Officer (CEO) or HA, or
-
With an attached email of approval from the CEO or HA.
-
-
By approving the mobile phone request, the CEO, HA, or designee, acknowledges approval to incur monthly charges for the phone line in their institutional or program budget.
-
-
Transferring a Mobile Phone
-
The CEO or HA may request the transfer of a mobile phone between staff in the same CCHCS institution or program and billing unit by submitting a request through the Solution Center. The ITSD is responsible for completing the transfer request following the CCHCS IT Asset Transfer Process.
-
-
Deactivating and Returning a Mobile Phone
-
Following the CCHCS Employee Separation Process, when staff with a CCHCS-issued mobile phone separate from CCHCS, the supervisor shall submit a ServiceNow request to deactivate the device prior to the separation date. The supervisor shall ensure the mobile phone is returned to the ITSD.
-
The IT Desktop Support technician shall update the ServiceNow request when the phone is received.
-
-
Security
-
Physical Security
-
CCHCS mobile phone users shall take reasonable steps to prevent damage or loss to the mobile phone.
-
Mobile phones shall not be left unattended and be stored securely in a locked location when not in use.
-
Staff shall follow all applicable regulatory and traffic laws while using the mobile phone.
-
-
Data Security
-
CCHCS mobile phone users shall:
-
Take reasonable steps to protect the mobile phone from cybersecurity threats and attacks.
-
Use a passcode to protect the mobile phone.
-
Ensure automatic software updates are turned on and mobile phones are updated to the most current software operating system to ensure access to new software patches.
-
-
-
-
Lost, Stolen, or Damaged Mobile Phone
-
Staff shall follow the procedure documented in the Health Care Department Operations Manual (HCDOM), Section 5.3.1, Lost and Stolen Assets.
-
Report all possible security incidents (e.g., lost or stolen information or mobile phone) as detailed on the Information Security Office SharePoint site.
-
Staff shall report any damage to their mobile phone immediately by submitting a ticket to the IT Solution Center.
-
-
Usage and Restrictions
-
CCHCS-issued mobile phones shall be used for CCHCS business only pursuant to HCDOM, Section 5.3.15, Acceptable Use.
-
All CCHCS mobile phones are issued with the camera enabled. Mobile phone users shall adhere to the HCDOM, Section 5.3.2, Camera Use, when utilizing the camera.
-
Only CCHCS-approved applications may be downloaded from the CCHCS Catalog on mobile phones.
-
CCHCS mobile phone users shall not change any configurations or standard features.
-
Any unauthorized disabling of or tampering with configuration or installed software shall be subject to corrective or disciplinary action in accordance with CCR, Title 15, Section 3392, et seq. and Department Operations Manual, Chapter 3, Article 22, Employee Discipline, Sections 33030.8, 33030.9, 33030.15.
-
Employees shall report any violations of this policy to their supervisor.
-
-
Shared Usage
-
Mobile phones may be assigned to an individual for use on a shared basis for a designated function by a CCHCS service unit.
-
In the instance a mobile phone is used on a shared basis, it shall be assigned to the person responsible for the group, and this individual shall be accountable for the device.
-
-
-
References
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 1, Article 13, Section 13010 – Public/Media Information
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 2, Article 12, Section 22030.12.1 Sensitive Property
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 41, Section 48010.5 – Acceptable Uses and Ethics
-
Health Care Department Operations Manual, Chapter 5, Article 3, Section 5.3.1, Lost and Stolen Assets
-
Health Care Department Operations Manual, Chapter 5, Article 3, Section 5.3.2, Camera Use
-
Health Care Department Operations Manual, Chapter 5, Article 3, Section 5.3.15, Acceptable Use
-
-
Revision History
-
Effective: 06/16/2023
-
5.3.4 Digital Signature Security
-
Policy
-
Any use of digital signature technology within California Correctional Health Care Services (CCHCS) must comply with all requirements stated in the California Government Code Section 16.5 and California Code of Regulations, Title 2, Division 7, Chapter 10, Digital Signatures. This information can be reviewed at: https://www.sos.ca.gov/administration/regulations/current-regulations/technology/digital-signatures/government-code-16-5 and https://www.sos.ca.gov/administration/regulations/current-regulations/technology/digital-signatures.
-
Digital Signature Usage
-
The use of a digital signature shall have the same force and effect as the use of a manual signature if and only if it embodies all of the following attributes:
-
It is unique to the person using it.
-
It is capable of verification.
-
It is under the sole control of the person using it.
-
It is linked to data in such a manner that if the data are changed, the digital signature is invalidated.
-
-
-
Authorized Digital Signature Solutions
-
CCHCS authorizes the use of only Public Key Infrastructure (PKI) digital certificate based digital signature technology for the purposes of applying a digital signature to electronic forms or documents.
-
-
Approved PKI Solutions
-
All PKIs that are used to produce digital certificates to create digital signatures for official CCHCS transactions must be approved by the California Secretary of State. The approved list of PKI vendors can be found at: https://www.sos.ca.gov/administration/regulations/current-regulations/technology/digital-signatures/approved-certification-authorities/.
-
-
Approved Digital Certificate Algorithms
-
Digital certificates that are intended to apply digital signatures must comply with FIPS 186-2 standards. FIPS 186-2 requires that one of the following digital signature (ds) algorithms by employed: Digital Signature Algorithm (DSA), RSA (Rivest, Shamir and Adleman), or ECDSA (Elliptical Curse Digital Signature Algorithm).
-
-
-
-
Purpose
-
This policy is intended to detail the requirements for the developing and/or using digital signature technology with CCHCS systems and data.
-
-
Applicability
-
This policy applies to all CCHCS Information Technology (IT) assets and/or anyone that accesses or uses any CCHCS IT asset.
-
-
Responsibility
-
All CCHCS Employees and Contractors are responsible for:
-
Reviewing and understanding this policy as it relates to their job role and responsibilities
-
Complying with all policy provisions
-
Communicating any risks or issues associated with the effectiveness of this policy and/or its enforcement to the CCHCS Office of Information Security (OIS)
-
Immediately reporting any known areas of non-compliance to the CCHCS OIS
-
-
Information Security Officer (ISO) is responsible for:
-
Authoring and enforcing this CCHCS Information Security Policy
-
Developing a performance metric to help articulate the organizational value of this policy and its effectiveness
-
Reporting policy performance metrics to the Chief Information Officer (CIO)
-
Managing the annual enterprise information security policy update process and ensuring tasks are completed effectively and on time
-
-
Organizational Unit Managers are responsible for:
-
Reviewing and understanding this policy as it relates to the objectives and operations of their organizational unit
-
Continually assessing the effectiveness of this policy as it relates to their organizational unit’s objectives and operations and reporting any issues or risks to CCHCS’s ISO
-
Promoting policy awareness, understanding, and compliance within their organizational business unit
-
Immediately reporting any known areas of non-compliance to the CCHCS OIS
-
-
CIOs are responsible for:
-
Reviewing and approving this policy
-
Promoting policy awareness, understanding, and compliance throughout the organization
-
Ensuring necessary resources are provided to support policy development, implementation, and compliance efforts
-
-
-
Procedure
-
Digital Certifcates
-
Digital Certificate Storage: CCHCS requires that all digital certificates that will be used for digital signatures must be stored on a FIPS 140-2 certified Smart Card device. The Smart Card must also be configured to require a PIN to access the digital certificate stored on the Smart Card.
-
Certificate Revocation Verification: Prior to applying a digital signature to an electronic document, the validity of the digital certificate used to apply the digital signature must be verified by performing a Certificate Revocation List (CRL) lookup.
-
CRL Publishing: Any PKI deployed to support digital signature must update the associated CRL to an Internet accessible HTTP website at least once every 24 hours.
-
Identity Proofing Requirements for Digital Certificate Requests: All CCHCS employees or contractors that require a digital certificate to apply a digital signature for CCHCS transactions must have their identity verified to ensure the requester is who he or she claims to be. CCHCS requires the verification process to include at least one in-person or face-to-face meeting whereby the requester presents an official U.S. Government, Military, or State identification card to a CCHCS agent authorized to verify identity prior to receiving the digital certificate. If electronic verification is used as part of the ID proofing process the requester must be assigned a unique username and must be challenged to provide knowledge of a secret password that is known only by the requester.
-
-
Use and Application of Digital Signatures
-
Authorized Users of Digital Signature
-
Only users formally authorized by CCHCS management to use digital signature technology can apply a digital signature to a CCHCS IT asset. Formal authorization can be achieved by completing a Digital Signature Request form, having it signed by designated CCHCS management, and having it stored on file for audit retrieval purposes. The Digital Signature Request form is available through CCHCS IT Division.
-
-
Authorized Usage of Digital Signature
-
Digital signatures can only be used with those IT assets that have been formally authorized by CCHCS management for use with digital signature technology.
-
-
Applying a Digital Signature
-
When applying a digital signature, controls must be in place to ensure user credentials are valid and verified. Controls must also be in place to ensure all communications between the application and the Smart Card containing the digital certificate are appropriate secured and encrypted.
-
-
Lost or Stolen Smart Cards
-
All lost or stolen Smart Cards must be reported to the ISO immediately and no longer than 24 hours from the time it is recognized the Smart Card is missing.
-
-
-
Enforcement, Auditing, and Reporting
-
Violation of CCHCS’s enterprise information security policies by an employee or contractor may result in immediate revocation of access rights to CCHCS’s IT assets. Additionally violations of security policies are subject to disciplinary action. The specific disciplinary action that shall be taken depends upon the nature of the violation and the impact of the violation on the CCHCS’s information and/or data assets and related facilities. A partial list of potential disciplinary actions follows:
-
Written reprimand
-
Suspension without pay
-
Reduction in pay
-
Demotion
-
Dismissal
-
Criminal prosecution (misdemeanor or felony, State or federal).
-
-
CCHCS reserves the right to consider legal remedies, or prosecution, against any person or entity for violations of any Law or regulatory compliance matter.
-
-
-
Review and Approval
-
This policy is approved by CCHCS’s CIO and will remain authorized and enforceable until replaced by an updated version. This policy will be reviewed annually by CCHCS’s ISO to ensure that it stays current. Changes to this policy will only be applied by CCHCS’s ISO. All CCHCS employees and contractors may submit suggested changes for the policy to the ISO in writing. The ISO may use the suggestions as part of the annual policy review and update process. The primary dissemination vehicle for the CCHCS Information Security Policies will be the CCHCS Intranet.
-
-
Resources
-
For questions or clarification please contact CCHCS OIS at CCHCS-ISO@cdcr.ca.gov.
-
-
References
-
California Government Code Section 16.5
-
California Code of Regulations, Title 2, Division 7, Chapter 10, Digital Signatures
-
-
Revision History
-
Effective: 03/2011
Revised: 03/07/2023
-
5.3.5 Electronic Mail Retention
-
Policy
-
California Correctional Health Care Services (CCHCS), Information Technology Services Division (ITSD) shall retain all sent and received electronic mail (e-mail) from the CCHCS E-mail System regardless of whether it has been opened or not, for a period of three years. E-mail messages are subject to federal and state laws.
-
-
Purpose
-
The purpose of this policy is to establish parameters to effectively capture, manage, and retain e-mail messages. Policy guidelines cover information that is either stored or shared via e-mail, including e-mail attachments.
-
-
Applicability
-
This policy applies to all CCHCS staff utilizing the CCHCS E-mail System network.
-
-
Responsibility
-
CCHCS’s Chief Information Officer shall authorize and enforce this policy.
-
Organizational users shall review, understand, and comply with this policy.
-
ITSD shall ensure adequate processes and procedures are in place to comply with policy directives.
-
-
Control and Maintenance
-
If litigation is pending or future litigation is reasonably probable, the law imposes a duty upon CCHCS to preserve all documents and records that pertain to the litigation. A litigation hold directive overrides any retention policy until the litigation has been cleared.
-
This policy specifies the period for which CCHCS ITSD shall retain e-mails but does not supersede the record retention schedule of any area of CCHCS. Each area of CCHCS is responsible for ensuring retention of records in compliance with that area’s own record retention schedule.
-
This policy shall be reviewed annually by CCHCS ITSD to ensure compliance with federal and state law.
-
CCHCS employees and contractors may submit inquiries regarding the policy to ITSD by submitting an Information Technology Solution Center ticket.
-
-
References
-
California Government Code, Title 1, Division 7, Chapter 3.5, Inspection of Public Records, Article 1, Section 6250-6265
-
California Penal Code, Part 4, Title 3, Chapter 2, Criminal Offender Record Information, Section 13100-13104
-
California Code of Regulations, Title 15, Division 3, Chapter 1, Subchapter 4, Article 1, Section 3261.2, Authorized Release of Information
-
California State Administrative Manual, Section 5320, Training and Awareness for Information Security and Privacy
-
Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 1, Article 16, Section 13040.11.1, Retention of Public Records Act Requests
-
Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 36, Section 47090.10, Instant Messaging Retention
-
Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 38, Section 47110.16, E-Mail Retention
-
-
Revision History
-
Effective: 01/2017
Reviewed: 03/07/2023
-
5.3.6 Information Security Policy Development and Maintenance
-
Policy
-
California Correctional Health Care Services (CCHCS) has adopted the following principles to govern information security policy development and maintenance.
-
Risk will be identified, assessed, and managed
-
Risk tolerance levels will be constantly recalibrated
-
Accountability over assets will be established
-
Least privilege principle will be used to determine the degree of access
-
Incompatible responsibilities will be separated
-
Information and system integrity, confidentiality and availability will be maintained
-
Personal privacy will be addressed
-
Ethical behavior will be practiced
-
IT Systems will be compliant with all applicable legal, statutory, and regulatory requirements
-
-
-
Purpose
-
Information security policies express CCHCS management’s requirements for appropriately protecting enterprise Information Technology (IT) assets. Information security policies are meant to address all applicable organizational, business, legal, and regulatory information security requirements that are necessary to help ensure the confidentiality, integrity, and availability of CCHCS’s IT assets. The objective of this policy is to explain the process used to develop and maintain CCHCS information security policies.
-
-
Applicability
-
This policy applies to all CCHCS IT assets and/or anyone that accesses or uses any CCHCS IT asset.
-
-
Responsibility
-
All CCHCS Employees and Contractors are responsible for:
-
Reviewing and understanding this policy as it relates to their job role and responsibilities
-
Communicating any risks or issues associated with the effectiveness of this policy and/or its enforcement to the CCHCS Office of Information Security (OIS)
-
Immediately reporting any known areas of non-compliance to the CCHCS OIS
-
-
ISO is responsible for:
-
Authoring and enforcing this CCHCS information security policy
-
Developing a performance metric to help articulate the organizational value of this policy and its effectiveness
-
Reporting policy performance metrics to the Chief Information Officer (CIO)
-
Managing the annual enterprise information security policy update process and ensuring tasks are completed effectively and on time
-
-
Organizational Unit Managers are responsible for:
-
Reviewing and understanding this policy as it relates to the objectives and operations of their organizational unit
-
Continually assessing the effectiveness of this policy as it relates to their organizational unit’s objectives and operations and reporting any issues or risks to CCHCS’s ISO
-
Promoting policy awareness, understanding, and compliance within their organizational business unit
-
Immediately reporting any known areas of non-compliance to the CCHCS OIS
-
-
CIO is responsible for:
-
Reviewing and approving this policy
-
Promoting policy awareness, understanding, and compliance throughout the organization
-
Ensuring necessary resources are provided to support policy development, implementation, and compliance efforts
-
-
-
Procedure
-
Information Security Policy Development
-
By the final business day of January each year, CCHCS CIO will appoint an Information Security Policy Review (ISPR) Committee. The ISPR Committee must include sufficient members to appropriately represent the enterprise in an effective and efficient manner. This committee will be accountable for representing and addressing information security policy development and maintenance activities. Each member will be accountable for ensuring their organizational unit’s information security policy requirements are addressed. CCHCS’s ISO is responsible for managing the information security policy development process.
-
-
Information Security Policy Review
-
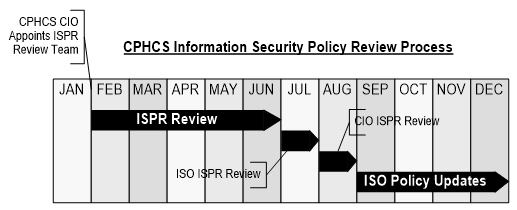
The appointed CCHCS ISPR Committee will meet regularly throughout the first half of the calendar year to assess the effectiveness and efficiency of existing information security policies, develop proposed changes to information security policies, and produce final proposed policy changes to the ISO by the final business day in June. The ISO will review all proposed policy changes and will produce a final set of recommended policy changes to the CIO by the final business day in July. The CIO will review the recommended policy changes and will provide his or her final approvals to the ISO by the final business day in August. The ISO will incorporate all approved policy changes into new policy versions and will manage the iterative release cycle. The iterative release cycle must ensure proper document versioning and change management procedures to capture any policy changes and provide a repository of previous versions. The iterative release process must also include updating any information security policy education and awareness components and effectively communicating any policy changes to the enterprise user population. This policy review cycle is outlined in the graphic below.
-
-
Information Security Policy Implementation
-
Authorized policy version updates will go into effect starting January 1st of each calendar year.
-
-
Information Security Policy Awareness, Understanding, and Accountability
-
All new CCHCS employees and contractors must sign an information security policy statement of compliance and accountability document before accessing any CCHCS IT assets. The statement of compliance and accountability document is meant to indicate that a signee: a) is aware of CCHCS’s information security policies, b) understands how to comply with CCHCS’s information security policies, and c) is accountable for ensuring compliance with CCHCS information security policies. In addition to the original signing of the statement of compliance and accountability, all CCHCS employees and contractors must resign the statement of compliance and accountability annually. Information security policies must be made available to any authorized requestor.
-
-
Enforcement
-
Violation of CCHCS’s information security policies by an employee or contractor may result in immediate revocation of access rights to CCHCS’s IT assets. Violations of security policies are subject to disciplinary action. The specific disciplinary action that shall be taken depends upon the nature of the violation and the impact of the violation on the CCHCS’s IT assets and related facilities. A partial list of potential disciplinary actions follows:
-
Written reprimand
-
Suspension without pay
-
Reduction in pay
-
Demotion
-
Dismissal
-
Criminal prosecution (misdemeanor or felony, State or federal)
-
-
CCHCS reserves the right to consider legal remedies, or prosecution, against any person or entity for violations of any law or regulatory compliance matter.
-
-
-
Review and Approval
-
This policy is approved by CCHCS’s CIO and will remain authorized and enforceable until replaced by an updated policy version. This policy will be reviewed annually by CCHCS’s ISO to ensure that it is current. Changes to this policy will only be applied by CCHCS’s ISO. All CCHCS employees and contractors may submit suggested changes for the policy to the ISO in writing. Upon due consideration, the ISO may use the suggestions as part of the annual review and update of the policy. The primary dissemination vehicle for the CCHCS information security policies will be the CCHCS Intranet.
-
-
Resources
-
For questions or clarification please contact CCHCS OIS at CCHCS-ISO@cdcr.ca.gov.
-
-
Revision History
-
Effective: 01/2011
Revised: 03/07/2023
-
5.3.10 Change And Configuration Management
-
Introduction and Overview
-
Business functions are highly dependent on secure and stable Information Technology (IT) operating environments. Secure and reliable IT environments are enabled through both maintaining standard configurations and establishing processes and procedures to effectively manage changes to the operating environments.
-
The goal of formalized IT change management is to facilitate IT changes as defined in enterprise standards, guidelines, and procedures while minimizing negative impacts to the organization.
-
The goal of IT configuration management is to establish, implement, and manage information asset baseline configurations and maintain consistency throughout the system lifecycle.
-
This policy establishes California Department of Corrections and Rehabilitation, California Correctional Health Care Services, and California Prison Industry Authority (hereinafter referred to as department) requirement for formal change and configuration management.
-
-
Objectives
-
The objective for this policy is to establish department requirements for standardized methods and procedures for the management of information asset configurations and changes to department information and technology environments, while integrating security and risk considerations.
-
-
Scope and Applicability
-
The scope of this policy extends to all State information assets owned and operated by the department, information assets managed by third parties on behalf of the department, and all information assets that process or store department information in support of department services and mission.
-
This policy applies to Owners of Information Assets and Information Asset Custodians.
-
-
Policy Directives
-
The department shall:
-
Formally manage all changes to information assets.
-
Utilize the Change Control Board, which includes a change advisory board that meets on a regular basis to review changes to information assets.
-
Ensure that the change advisory board comprises representation from appropriate stakeholders, and in particular from impacted business areas.
-
Ensure that the change advisory board includes formal security representation, and that change management processes formally integrate security evaluations and risk impact assessments in all change activities.
-
Establish comprehensive enterprise-wide change management, comprised of supporting processes, workflows, and a centralized repository for all changes, including changes to baseline configurations.
-
Establish, implement, and manage department operating baselines for information asset configurations.
-
Establish and implement technologies, processes, and procedures to maintain and manage information asset configurations.
-
Ensure third parties and contractors are subject to change and configuration management policies, discipline, and practices. Any changes to department information assets proposed by service providers, regardless of whose environment they operate in, shall be governed by department change and configuration management processes.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all Owners of Information Assets, Information Asset Custodians, and users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every 2 years.
-
-
Department Information Security Officer (ISO):
-
Shall assist Owners of Information Assets and Information Asset Custodians in the identification of data security controls and processes.
-
Shall ensure that data security controls, methods, and processes meet department and applicable regulatory requirements for security.
-
-
Department Owners of Information Assets and Program Management:
-
In collaboration with the Information Asset Custodians shall ensure that this policy and its directives are implemented and enforced.
-
-
Department Information Asset Custodians:
-
Shall implement configuration and change management technology, process, and workflow controls as approved by Owners of Information Assets.
-
Shall maintain change and configuration management records for a minimum period of 12 months. Secure deletion or destruction of these records shall be in accordance with the records retention schedule.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards, and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal.
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with the State of California Government Code section 11549.3.
-
-
Revisions
-
The CIO or Designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual, 19C, Project Approval Lifecycle Stage 3 – Solution Development
-
Statewide Information Management Manual, Sections 58C, 58D, 66B, 5305-A, 5310-A and B; 5325-A and B; 5330-A, B, and C; 5340-A and C; and 5360-B
-
State Administrative Manual, Section 5315, Information Security Integration
-
State Administrative Manual, Section 5315.5, Configuration Management
-
State Administrative Manual, Section 5355, Endpoint Defense
-
National Institute of Standards and Technology, Special Publications 800-53, Configuration Management, CM-2, CM-3, CM-4, CM-5, CM-6, CM-9
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 45, Section 49020.9
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 02/2022
-
5.3.11 Endpoint Security
-
Introduction and Overview
-
Department information assets are often used to conduct business functions internally as well as with other State and non-department persons and devices on the Internet. Devices used for such department business purposes are comprised of servers, network devices, and end user devices including mobile computers, tablets, and smart phones; such devices are collectively called “endpoints” or “endpoint devices.” Some department information assets are more prone to loss or theft due to their size, mobility, or location of use.
-
The department needs to ensure that endpoints are suitably protected to prevent unauthorized access to data and information that may reside on the endpoints.
-
-
Objectives
-
Objectives for this policy are to define the requirements to protect department endpoints that may routinely interact with unknown or untrusted devices on the Internet, or that are more susceptible to loss or theft.
-
-
Scope and Applicability
-
The scope of this policy extends to all State information assets owned and operated by the department, information assets managed by third parties on behalf of the department, and all information assets that process or store department information in support of department services and mission.
-
This policy applies to Owners of Information Assets and Information Asset Custodians.
-
-
Policy Directives
-
The department shall ensure that:
-
All department endpoints are identified and endpoint asset inventories are documented and continually updated.
-
Risks to individual department endpoint device types and the data they access, process, and store are assessed.
-
The requisite endpoint protection controls, as referenced in the Statewide Information Management Manual, are implemented and maintained to mitigate risks to each endpoint.
-
Endpoint protection controls include people (asset users), processes, and technology controls.
-
Endpoint protection controls are continuously monitored.
-
Endpoint protection controls are reviewed at least annually.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all Owners of Information Assets, Information Asset Custodians, and users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every 2 years.
-
-
Department Information Security Officer (ISO):
-
Shall assist Owners of Information Assets and Information Asset Custodians with the identification and selection of endpoint protection controls.
-
Shall ensure that endpoint protection controls meet department requirements for security and privacy.
-
-
Department Owners of Information Assets and Program Management:
-
In collaboration with the Information Asset Custodians shall ensure that the endpoint protection controls are defined, documented, and implemented, and that implementation is reviewed annually.
-
In collaboration with the Information Asset Custodians shall ensure the endpoint protection controls commensurate with the sensitivity or criticality of the asset are implemented for assets under their purview.
-
-
Department Information Asset Custodians:
-
Shall implement the requisite endpoint protection controls based upon the sensitivity or criticality of the assets as defined by the Owners of Information Assets.
-
Shall maintain and update endpoint protection technologies based on best practices.
-
Shall maintain records of endpoint protection controls and ensure proper change management.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards, and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal.
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with the State of California Government Code section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual, 5305-A, Information Security Program Management Standard
-
Statewide Information Management Manual, 5355-A, Endpoint Protection Standard
-
State Administrative Manual, Section 5355, Endpoint Defense
-
State Administrative Manual, Section 5355.1, Malicious Code Protection
-
National Institute of Standards and Technology, Special Publications 800-53, Security Assessment and Authorization, CA-7
-
National Institute of Standards and Technology, Special Publications 800-53, Configuration Management, CM-2, CM-3, CM-6, CM-7, CM-10, CM-11
-
National Institute of Standards and Technology, Special Publications 800-53, System and Communications Protection, SC-8, SC-10, SC-11, SC-13, SC-18, SC-23, SC-24, SC-28, SC-38, SC-42, SC-43
-
National Institute of Standards and Technology, Special Publications 800-53, System and Information Integrity, SI-2, SI-3, SI-4, SI-5, SI-7, SI-8, SI 11
-
National Institute of Standards and Technology, Special Publications 800-53, Program Management, PM-9
-
National Institute of Standards and Technology, Special Publications 800-53, Risk Assessment, RA-2, RA-3, RA-5
-
National Institute of Standards and Technology, Special Publications 800-53, Physical and Environmental Protection, PE-3, PE-19, PE-20
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 41, Section 48010.5
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 02/2022
-
5.3.12 Security Analytics And Continuous Monitoring
-
Introduction and Overview
-
Information technology environments that support department business functions and services are complex and dynamic computer network environments, which process, manipulate, and store large amounts of data and information. In order to detect unexpected and suspicious activities and events within such complex networks, it is important to continuously monitor computing environments. Continuous monitoring allows the department to rapidly identify anomalous or suspicious activities and events, analyze these events, and respond accordingly.
-
-
Objectives
-
The objective for this policy is to define department requirements for continuous monitoring of department networks and information assets for signs of malicious use, anomalies, and unexpected behavior and usage patterns.
-
-
Scope and Applicability
-
The scope of this policy extends to all State information assets owned or operated by the department, and governs the facilities and information assets owned or operated on behalf of the department by business partners and service providers.
-
This policy applies to Owners of Information Assets and Information Asset Custodians.
-
-
Policy Directives
-
The department shall ensure that:
-
A strategy for security analytics and continuous monitoring will be defined, documented, and implemented.
-
The strategy will be based on security risk management principles in order to determine optimal monitoring locations, methods, and techniques.
-
The department’s security analytics and continuous monitoring strategy will be integrated with the department’s security and event logging and monitoring strategy, threat assessments, and security analytics and event correlation.
-
The department’s continuous monitoring is linked to incident response management and other department incident management processes.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all Owners of Information Assets, Information Asset Custodians, and users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually, and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every 2 years.
-
-
Department Information Security Officer (ISO):
-
Shall assist Owners of Information Assets and Information Asset Custodians with the implementation of this policy.
-
Shall assist Owners of Information Assets and Information Asset Custodians in the analysis and assessment of risks posed by anomalous activities or identified events.
-
-
Department Owners of Information Assets and Program Management:
-
In collaboration with the Information Asset Custodians shall ensure that this policy is implemented and implementation is reviewed annually.
-
-
Department Information Asset Custodians:
-
Shall implement technology and process controls.
-
Shall maintain records of security monitoring controls implemented.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in DOM Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards, and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal.
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with the State of California Government Code section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
State Administrative Manual, Section 5335, Information Security Monitoring
-
State Administrative Manual, Section 5335.1, Continuous Monitoring
-
State Administrative Manual, Section 5335.2, Auditable Events
-
National Institute of Standards and Technology, Special Publications 800-53, Audit and Accountability, AU-2, AU-6, AU-7, AU-13
-
National Institute of Standards and Technology, Special Publications 800-53, Incident Response, IR-5, IR-10
-
National Institute of Standards and Technology, Special Publications 800-53, Physical and Environmental Protection, PE-6
-
National Institute of Standards and Technology, Special Publications 800-53, Program Management, PM-9
-
National Institute of Standards and Technology, Special Publications 800-53, Risk Assessment, RA-2, RA-3
-
National Institute of Standards and Technology, Special Publications 800-53, Security Assessment and Authorization, CA-7
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 41, Section 48010.5
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 02/2022
-
5.3.13 Server Configuration
-
Introduction and Overview
-
This document defines the policy for all servers, physical and virtual, owned or operated by the department. Effective implementation of this policy minimizes the risk of server vulnerabilities that can result in system unavailability, data corruption, unauthorized access, information and resource misuse, and service disruption.
-
-
Objectives
-
The objective of this policy is to establish the base configuration of internal server equipment that is owned and operated by the department. Effective implementation of this policy will minimize unauthorized access to department proprietary information and technology.
-
-
Scope and Applicability
-
The scope of this policy extends to all information assets owned or operated by the department, including critical infrastructure, as well as information assets owned or operated by third-parties on behalf of the department.
-
This policy applies to Owners of Information Assets and Information Asset Custodians.
-
-
Policy Directives
-
The department shall:
-
Only create server service accounts when necessary.
-
Use the Principle of Least Privileged to limit user access rights to a minimum.
-
Not use administrative accounts (e.g., root, administrator, O365 Global) when a non-privileged account will suffice.
-
Disable/lock/delete all accounts except those required to provide necessary services.
-
Change the default passwords for all accounts and follow password security best practices outlined in Statewide Information Management Manual (SIMM) 5300-A, Org-Defined Standards, (National Institute of Standards and Technology [NIST] IA-5(1)).
-
Limit access to administrative accounts to only those who have operational need and have been authorized.
-
Ensure service accounts are not part of Local Administrators or Domain Administrator accounts.
-
Authorize and document all administrative (privileged) accounts.
-
Encrypt all passwords and all sensitive and confidential data while in transit. Passwords shall adhere to State Org-Defined Policy. (See State Administrative Manual [SAM] 5350.1, SIMM 5300-B and NIST, Special Publications [SP] 800-63B, FIPS 140-2).
-
Authenticate users over encrypted protocols.
-
Log all access to the server and services that are protected through access control methods.
-
Establish and implement controls to ensure that service account functions are authorized using service account credentials only.
-
-
Systems Configuration and Maintenance
-
Servers shall be patched and hardened before attaching them to the network. Security patches shall be installed on the system not less than monthly. If an intelligence source advises of an imminent threat, patches shall be installed according to documented information technology standards.
-
Servers shall be physically secured in locations accessible only to authorized personnel.
-
Only required services shall be enabled or installed on the server. Services that are not required shall be uninstalled or disabled.
-
Regular back-ups of the server shall be completed according to the back-up and retention policy and tested on a periodic schedule.
-
-
Monitoring
-
The server shall capture and archive critical user, network, system, and security event logs to enable review of system data for forensic and recovery purposes.
-
Security-related events shall be reviewed and investigated. Events include, but are not limited to:
-
Account lockouts
-
Failed user account logins
-
Evidence of unauthorized access to privileged accounts
-
Anomalous occurrences that are not related to specific applications on the server
-
-
Security incidents shall be handled immediately in accordance with SAM and SIMM and reported to the department Information Security Officer (ISO), the data owners or their designees.
-
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all Owners of Information Assets, Information Asset Custodians, and users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually, and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every 2 years.
-
-
Department ISO:
-
Shall assist Owners of Information Assets and information asset custodians in the identification of data security controls and processes.
-
Shall ensure data security controls, methods, and processes meet department and applicable regulatory requirements for security.
-
Shall participate in all incidents involving information security.
-
-
Department Owners of Information Assets and Program Management:
-
In collaboration with the Information Asset Custodians, shall ensure that this policy is implemented and implementation is reviewed annually and as appropriate.
-
Shall audit user access rights and privileges to ensure alignment with individual job roles and functions on an annual or more frequent basis as appropriate.
-
-
Department Information Asset Custodians:
-
Shall review accounts with privileged access no less than semi-annually and verify that continued privileged access is required.
-
In collaboration with Owners of Information Assets, shall ensure the information security control measures are commensurate with the sensitivity or criticality of information assets under their purview.
-
Shall assist Owners of Information Assets in identifying data security controls commensurate with the classification of the data.
-
Shall document, implement, monitor, and maintain data security protection controls based upon the sensitivity or criticality of the assets.
-
Shall develop and implement tools, technologies, processes, and procedures to support, monitor, and maintain data security controls.
-
Shall maintain data security records.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the California Deparmtent of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards, and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with the State of California Government Code section 11549.3.
-
-
Revisions
-
The CIO or Designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual, Section 5300-B, Foundational Framework
-
Statewide Information Management Manual, Section 5305-A, Information Security Program Management Standard
-
State Administrative Manual, Section 5305.5, Information Asset Management
-
State Administrative Manual, Section 5310.4, Individual Access to Personal Information
-
State Administrative Manual, Section 5310.6, Data Retention and Destruction
-
State Administrative Manual, Section 5310.7, Security Safeguards
-
State Administrative Manual, Section 5340, Information Security Incident Management
-
State Administrative Manual, Section 5340.1, Incident Response Training
-
State Administrative Manual, Section 5340.2, Incident Response Testing
-
State Administrative Manual, Section 5340.3, Incident Handling
-
State Administrative Manual, Section 5340.4, Incident Reporting
-
State Administrative Manual, Section 5350.1, Encryption
-
State Administrative Manual, Section 5365, Physical Security
-
State Administrative Manual, Section 5365.1, Access Control for Output Devices
-
State Administrative Manual, Section 5365.2, Media Protection
-
State Administrative Manual, Section 5365.3, Media Disposal
-
Federal Information Processing Standards, FIPS 199
-
Federal Information Processing Standards, FIPS 140-2
-
National Institute of Standards and Technology, Special Publications 800-53, Access Control, AC-3, AC-4
-
National Institute of Standards and Technology, Special Publications 800-53, Audit and Accountability, AU-2, AU-3, AU-13
-
National Institute of Standards and Technology, Special Publications 800-53, Configuration Management, CM-8
-
National Institute of Standards and Technology, Special Publications 800-53, Identification and Authentication, IA-5(1)
-
National Institute of Standards and Technology, Special Publications 800-53, Media Protection, MP-1, MP-2, MP-3, MP-4, MP-5, MP-6, MP-7
-
National Institute of Standards and Technology, Special Publications 800-53, Physical and Environmental Protection, PE-5, PE-19, PE-20
-
National Institute of Standards and Technology, Special Publications 800-53, Planning, PL-4
-
National Institute of Standards and Technology, Special Publications 800-53, Program Management, PM-9
-
National Institute of Standards and Technology, Special Publications 800-53, Risk Assessment, RA-2, RA-3
-
National Institute of Standards and Technology, Special Publications 800-53, Security and Communications Protection, SC-4, SC-8, SC-13, SC-17, SC-28
-
National Institute of Standards and Technology, Special Publications 800-63B, Digital Identity Guidelines, Authentication and Lifecycle Management
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 41, Section 48010.5
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 02/2022
-
5.3.14 Access Control
-
Introduction and Overview
-
Information assets owned by the California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA) are strategic assets intended for official business use, and are entrusted to State personnel and business partners in the performance of their job related duties.
-
Access may enable or restrict the ability to do something with a resource. Access control, then, is the selective restriction of these abilities and is comprised of both physical and logical access.
-
-
Objectives
-
Objectives for this policy are to:
-
Enable the development and implementation of a CDCR, CCHCS, and CALPIA (hereinafter referred to as department) identity and access management strategy that comprehensively addresses all access to department information assets.
-
Document requirements for the appropriate control and management of physical and logical access to, and the use of department information assets.
-
Require the use of appropriate authentication methods based on the type and sensitivity of information assets being accessed.
-
Govern the use of privileged access rights, such as those assigned to Administrator and Privileged Accounts.
-
-
Scope and Applicability
-
This policy applies to all personnel; all information assets owned or operated by the department; and all forms of physical and logical access to department information assets, including using wired, wireless, and remote access network connections. All department personnel shall comply with this policy.
-
-
Policy Directives
-
Before department Information Technology infrastructure network access, users shall be identified and authenticated.
-
Users accessing sensitive or confidential information shall be appropriately provisioned before accessing department owned or operated information assets and associated facilities.
-
In the case of physical access to facilities, where access control is a manual process, authentication shall be accomplished by manual verification of an identity (e.g., photo ID).
-
-
Access to department information assets and associated permissions shall be approved by the respective department information asset owner.
-
Records of all user account creations, deletions, and changes to user access and permissions shall be maintained for a period of at least 12 months.
-
The department shall develop a comprehensive identity and access management strategy based on statutory and organizational business requirements, including:
-
Supporting unique identification, individual user types and groups, job roles and access methods.
-
Limiting access to information assets and associated facilities to authorized users, processes, or devices, and to authorized activities and transactions.
-
Defining roles and assigning responsibilities pertaining to access control tools, technologies and processes.
-
Developing and implementing standards, technologies and processes to support its access control strategy.
-
Formally defining and documenting user account types and groups, and access use cases, commensurate with employment responsibilities.
-
Employing multi-factor authentication for remote access, and risk-based user authentication methods to accommodate approved logical access use cases.
-
Publicly available or published access and authentication credentials, such as default credentials, anonymous credentials and guest credentials, shall not be re used, and shall be replaced as a matter of standard procedure.
-
Display a notification of system use or security warning banner message on each system that requires affirmative acknowledgement by the user before authentication.
-
-
The department shall ensure that access to non-active personnel is deactivated before or immediately after termination, as appropriate.
-
The department shall review and validate user access and associated access permissions and privileges at least every 12 months to ensure alignment with individual job roles and functions.
-
Certain department information technology support personnel and network administrators shall require specific privileges to perform their duties.
-
For all Administrators and Privileged Account holders, the department shall:
-
Identify and document all Administrator and Privileged Account holders.
-
Ensure that administrative and privileged accesses are granted to users through established or approved local provisioning processes.
-
Ensure that such users acknowledge the privileges and only use those accounts to fulfill the specific job responsibilities for which the privileges apply.
-
Ensure automated processes including service accounts with privileged access to information systems shall follow established standards for password rotation, limited access and auditing.
-
Review and validate the continued business need for all Administrator and Privileged Accounts on an annual basis or when staffing, resource, or job function changes occur.
-
-
-
User access and permissions shall be based on the principles of least privilege and separation of duties.
-
The department shall define and document all auditable system events related to data and information access that shall be recorded.
-
The department shall ensure access control management systems are configured to capture and record audit and security information related to access events.
-
Audit and security records shall be securely stored and protected against tampering; audit and security records shall be maintained for the period defined in the records retention schedule.
-
Monitoring and alerting of anomalous or suspicious activities and events is most effectively accomplished through automated and real-time reviews of audit and security logs.
-
The department shall implement suitable controls to monitor for unauthorized changes to user access. Where feasible, unauthorized changes shall generate automated alerts to notify responsible department individuals.
-
In the absence of automated monitoring and alerting, the department Information Security Officer (ISO) shall review access record reports on a quarterly basis. Access records include: new user account creation requests, user access revocation requests, active user lists, and user termination lists.
-
-
Roles and Responsibilities
-
The department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all users of department Information Assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually, and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every two years.
-
-
Department Owners of Information Assets and Program Management:
-
In collaboration with the Information Asset Custodians shall ensure that this policy is implemented and implementation is reviewed at minimum annually.
-
Shall audit and assess user access rights and privileges to ensure alignment with individual job roles and functions on an annual basis.
-
-
Department Information Asset Custodians:
-
Shall implement user access and associated rights and privileges as requested and approved by Owners of Information Assets.
-
In collaboration with Owners of Information Assets, shall periodically review accounts with elevated privileges and verify that continued privilege account access is required.
-
In collaboration with Owners of Information Assets shall ensure access technology and process controls are commensurate with the sensitivity or criticality of information assets under their purview.
-
Shall revoke or modify individual user access rights and privileges upon notification from the Owners of Information Assets.
-
Shall maintain access records consistent with the retention schedule.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards, and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible or is technically impossible, if existing policy currently in place already meets these requirements, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variation as defined by the department ISO.
-
-
Authority
-
This policy complies with California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual, Section 5305-A, Information Security Program Management Standard
-
State Administrative Manual, Section 5305.4, Personnel Management
-
State Administrative Manual, Section 5305.7, Risk Assessment
-
State Administrative Manual, Section 5315, Information Security Integration
-
State Administrative Manual, Section 5335, Information Security Monitoring
-
State Administrative Manual, Section 5335.1, Continuous Monitoring
-
State Administrative Manual, Section 5335.2, Auditable Events
-
State Administrative Manual, Section 5355, Endpoint Defense
-
State Administrative Manual, Section 5355.1, Malicious Code Protection
-
State Administrative Manual, Section 5360, Identity And Access Management
-
State Administrative Manual, Section 5360.1, Remote Access
-
State Administrative Manual, Section 5360.2, Wireless Access
-
State Administrative Manual, Section 5365.1, Access Control for Output Devices
-
National Institute of Standards and Technology, Special Publications 800-53, Access Control, AC-1, AC-2 (1)(2)(3)(4), AC-3, AC-4, AC-5, AC-6 (1)(2)(5)(9)(10), AC-7, AC-8, AC-11, AC-12, AC-14, AC-17(1)(2)(3)(4), AC-18(1), AC 19(5), AC-20(1)(2), AC-21, AC-22, AC-24
-
National Institute of Standards and Technology, Special Publications 800-53, Audit & Accountability, AU-3, AU-6, AU-7, AU-8, AU-9, AU-10, AU 11, AU-13
-
National Institute of Standards and Technology, Special Publications 800-53, Awareness & Training, AT-2
-
National Institute of Standards and Technology, Special Publications 800-53, Identification & Authorization, IA-1, IA-2, IA-3, IA-4, IA-5, IA-6, IA-7, IA 8, IA-9, IA-10, IA-11
-
National Institute of Standards and Technology, Special Publications 800-53, Risk Assessment RA-1, RA-2, RA-3
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual,, Chapter 4, Article 45, Section 49020.6.1, 49020.7.1, 49020.9, 49020.10
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 03/2022
-
5.3.15 Acceptable Use
-
Introduction and Overview
-
Information assets owned by the California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA) (including but not limited to department data and information, laptops, cell phones, and removable storage devices) are strategic assets intended for official business use, and are entrusted to State personnel in the performance of their job-related duties.
-
Inappropriate use of CDCR, CCHCS, and CALPIA (hereinafter referred to as department) information assets could negatively affect the confidentiality, integrity, or availability of the information, information systems, or other information assets of the department and the State of California. Consequently, it is important for all users to access or use information assets in a responsible, ethical, and legal manner that safeguards department data and information.
-
Additionally, the appropriate use of information assets benefits the State and the department by strengthening the protection of the department and its personnel and business partners from illegal or potentially damaging activities.
-
-
Objectives
-
This policy defines and establishes the requirements for the appropriate use and safeguarding of department information assets.
-
-
Ownership of Information
-
Data and information in hard copy format and that which is electronically created, sent, received, processed, or stored on information assets owned, leased, administered, or otherwise under the custody and control of the department are the property of the State. Any information, not specifically identified as the property of other parties and that is transmitted, processed, or stored on the department’s and business partner Information Technology facilities and resources (including e-mail, messages, and files) is considered the property of the department.
-
Individual access and use of department information assets is neither personal nor private. As such, department management reserves the right to monitor and log all employee use of department information assets with or without advanced notice.
-
-
Scope and Applicability
-
The scope of this policy extends to all information assets owned or operated by the department and to all personnel authorized to use these assets.
-
-
Policy Directives
-
The department shall ensure that users use and protect department information assets in accordance with this policy and applicable information security and privacy policies.
-
Department Unacceptable Use
-
The department shall ensure that users do not:
-
Use department information assets to engage in or solicit the performance of any activity that violates laws, regulations, rules, policies, standards, and other applicable requirements issued by the federal government, the State of California, and the department.
-
Use department information assets for personal enjoyment, private gain or advantage, personal gain, political activity, unsolicited advertising, unauthorized fundraising, or an outside endeavor not related to State business.
-
Engage in any activity that attempts to circumvent or alter the function of the department’s security controls (e.g., spoofing email, anonymous proxies, or unauthorized encryption), or other activities that may degrade the performance of information resources, or may deprive an authorized user access to department assets.
-
Share their work-related account(s), passwords, Personal Identification Numbers, security questions/answers, security tokens (e.g., smartcard, key fob), or similar information or devices used for authentication and authorization purposes.
-
Use department information assets to send or arrange to send emails or intentionally access sites that contain pornographic, racist, or offensive material, chain letters or unauthorized mass mailings, and malicious code.
-
Users shall not connect or otherwise attach unauthorized devices or equipment to the department network infrastructure.
-
-
-
Roles and Responsibilities
-
The department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every two years.
-
-
Department Information Asset Users:
-
Shall use and protect department information assets in accordance with this policy and applicable information security and privacy policies.
-
Shall report any security concerns pertaining to department information asset security of which they become aware to the department Information Security Officer (ISO), designee, appropriate security staff or their immediate supervisor. Security concerns with information assets may include unexpected software or system behavior, which could result in unintentional disclosure of information or exposure to security threats.
-
Shall report any suspected or actual activities or events indicating misuse or violation of this policy to the department ISO, designee, appropriate security staff or their immediate supervisor.
-
Shall be aware of and adhere to all department information security and privacy policies.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards, and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the department ISO.
-
-
Authority
-
This policy complies with California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual, Section 5305-A, Information Security Program Management Standard
-
State Administrative Manual, Section 5305.3, Information Security Roles and Responsibilities
-
State Administrative Manual, Section 5320.4, Personnel Security
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 41, Section 48010.5
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 03/2022
-
5.3.16 Firewall Configuration
-
Introduction and Overview
-
Network firewalls act as a communications buffer between internal and external devices while simultaneously keeping out unwanted users, viruses, worms, or other malicious programs trying to access the protected network. Firewalls and the technology and procedures that support them help protect internal networks and manage traffic in and out of California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA)’s network.
-
-
Objectives
-
The objective of this policy is to define how firewalls are to be configured, implemented, and managed within the CDCR, CCHCS, and CALPIA (hereinafter referred to as department).
-
-
Scope and Applicability
-
The scope of this policy extends to all information assets owned or operated by the department, including mission critical infrastructure and information assets owned or operated by third parties (if applicable) on behalf of the department.
-
This policy applies to the department Chief Information Officer or their designee, Information Technology functions, information security sections, owners of critical infrastructure, Agency and Department Information Security Officers, Technology Recovery Plan coordinators, and Information Asset Custodians.
-
-
Policy Directives
-
The department shall use a multi-layered approach to protect computer resources and assets. Network security design shall include firewall functionality at all places in the network where opportunities exist for outside exploitation. This may include placing a firewall in areas other than the network perimeter to provide an additional layer of security and protect devices that are placed directly onto external networks (i.e. the Demilitarized Zone [DMZ]) or between different trusted and untrusted segments of the network.
-
Firewall Configuration
-
The department shall:
-
Implement configurations that restrict all inbound and outbound traffic associated with untrusted wired/wireless networks and hosts.
-
Deny all traffic by default and only allow inbound and outbound traffic thru approved exceptions.
-
Disable unnecessary user accounts and default accounts (e.g. Administrator, Guest, etc.).
-
Disable all unused and unnecessary ports, protocols, and services before deployment into a production environment.
-
Implement a DMZ that limits inbound traffic to the internal trusted network and permits authorized publicly accessible services, protocols, and ports/services.
-
Log all changes to firewall configuration parameters, enabled services, and permitted connectivity paths for a period of one year. The department data retention procedures shall be followed.
-
Physically secure firewalls in a location accessible only to authorized personnel. The placement of firewalls in an open area within a general-purpose data center is prohibited.
-
-
-
Firewall Administration and Management
-
The following firewall management practices shall be utilized:
-
Configuration of rulesets and policies shall be managed through an internal change management process.
-
Firewall security logs shall be reviewed no less than every six months to detect any unauthorized entry attempts or network anomalies, and shall be retained for a period of one year.
-
All enterprise firewall rulesets shall be reviewed according to documented processes and procedures.
-
All new inbound and outbound connections requiring firewall rulesets to be applied shall have a valid business justification and the approval of the Information Asset Custodian on behalf of the Information Asset Owner.
-
Current security updates, patches, and anti-virus definitions shall be applied in accordance with documented standards, threat intelligence, and product/vendor guidance.
-
Administrative access shall be restricted to authorized and approved Information Asset Custodians and designated security personnel.
-
Access to management and administrative interfaces shall be available only from locations that are deemed appropriate.
-
-
Roles and Responsibilities
-
The department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every two years.
-
-
The department Information Security Officer (ISO) is responsible for the oversight and coordination of entity information security policies and procedures.
-
The department Owners of Information Assets and Program Management, in collaboration with the Information Asset Custodians, are responsible for ensuring the protection of information assets under their purview.
-
The department Information Asset Custodians:
-
In collaboration with the Information Asset Owners, are responsible for ensuring implementation of this policy and its directives.
-
Shall review firewall security logs in accordance with this policy.
-
Shall notify the department ISO and the asset owner shall a security incident occur.
-
-
The department Firewall Administrators are responsible for managing firewall policies, updates, upgrades, software, installations, as well as other network security solutions. As access and network requirements change, firewall policies shall be updated to reflect these changes.
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards, and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the department ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3 and State Administrative Manual-5350 Operational Security.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
State Administrative Manual, Section 5305.5, Information Asset Management
-
State Administrative Manual, Section 5310.4, Individual Access to Personal Information
-
State Administrative Manual, Section 5310.6, Data Retention and Destruction
-
State Administrative Manual, Section 5310.7, Security Safeguards
-
State Administrative Manual, Section 5340, Information Security Incident Management
-
State Administrative Manual, Section 5340.1, Incident Response Training
-
State Administrative Manual, Section 5340.2, Incident Response Testing
-
State Administrative Manual, Section 5340.3, Incident Handling
-
State Administrative Manual, Section 5340.4, Incident Reporting
-
State Administrative Manual, Section 5350.1, Encryption
-
State Administrative Manual, Section 5365, Physical Security
-
State Administrative Manual, Section 5365.1, Access Control for Output Devices
-
State Administrative Manual, Section 5365.2, Media Protection
-
State Administrative Manual, Section 5365.3, Media Disposal
-
Federal Information Processing Standard, FIPS 199
-
National Institute of Standards and Technology, Special Publications 800-53, Access Control, AC-3 Access Enforcement, AC-4 Information Flow Enforcement
-
National Institute of Standards and Technology, Special Publications 800-53, Audit and Accountability, AU-2 Event Logging, AU-3 Content of Audit Records, AU-13 Monitoring for Information Disclosure
-
National Institute of Standards and Technology, Special Publications 800-53, Configuration Management, CM-8 System Component Inventory
-
National Institute of Standards and Technology, Special Publications 800-53, Media Protection, MP-1, MP-2, MP-3, MP-4, MP-5, MP-6, MP-7
-
National Institute of Standards and Technology, Special Publications 800-53, Physical and Environmental Protection, PE-5 Access Control for Output Devices, PE-19 Information Leakage, PE-20 Asset Monitoring and Tracking
-
National Institute of Standards and Technology, Special Publications 800-53, Planning, PL-4 Rules of Behavior
-
National Institute of Standards and Technology, Special Publications 800-53, Program Management, PM-9 Risk Management Strategy
-
National Institute of Standards and Technology, Special Publications 800-53, Risk Assessment, RA-2 Security Categorization, RA-3 Risk Assessment
-
National Institute of Standards and Technology, Special Publications 800-53, Assessment, Authorization and Monitoring, CA-7 Continuous Monitoring
-
National Institute of Standards and Technology, Special Publications 800-53, System and Communications Protection, SC-4 Information in Shared Resources, SC-8 Transmission Confidentiality and Integrity, SC-13 Cryptographic Protection, SC-17 Public Key Infrastructure Certificates, SC-28 Protection of Information at Rest
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 45, Sections 49020.8, 49020.9 and 49020.10
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 03/2022
-
5.3.17 Physical and Environmental Protection
-
Introduction and Overview
-
Information assets owned by the California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA) (including but not limited to department data and information, servers, laptops, tablets, cell phones, and removable storage devices) are strategic assets intended for official business use, and they are entrusted to State personnel in the performance of their job related duties.
-
Restricting physical access to information assets reduces the potential for their damage and misuse. Implementing and maintaining environmental controls provides optimal operating conditions for information assets that are critical to CDCR, CCHCS, and CALPIA (hereinafter referred to as department) business functions.
-
-
Objectives
-
Objectives for this policy are to establish physical security and environmental protection control requirements to safeguard department information assets against unauthorized access, use, disclosure, disruption, modification, or destruction.
-
-
Scope and Applicability
-
The scope of this policy extends to all State information assets owned or operated by the department, and governs physical access to department information assets.
-
This policy applies to all department personnel.
-
-
Policy Directives
-
The department shall define the control requirements for the physical environmental protection of information assets.
-
The department shall implement, manage, monitor, and regularly maintain physical security and environmental protection controls to safeguard State information assets for which they have custodianship.
-
Personnel identification systems and facility access controls shall be implemented for all personnel and visitors. Access logs shall be reviewed at minimum annually.
-
Environmental controls shall be implemented in computer rooms and data centers, including but not limited to, temperature and humidity regulators, fire detection and suppression, and electrical power conditioning.
-
Supporting controls, processes, and procedures to control physical access (e.g., security gates), handling digital media, and emergency processes and procedures shall be implemented.
-
Service records of periodic maintenance of physical and environmental protection controls (e.g., heating/cooling unit servicing) and results of tests of environmental controls (e.g., power outage) shall be retained for a minimum of six months.
-
Security risks shall be identified, remediated, and reported to the department Information Security Officer (ISO).
-
-
Roles and Responsibilities
-
The department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every two years.
-
-
The department Owners of Information Assets and Program Management:
-
Shall formally approve and authorize access and revocation of access to information assets.
-
In collaboration with the Information Asset Custodians shall validate access to information assets under their purview on an annual basis, or when staffing, resource or job function changes occur.
-
In collaboration with the Information Asset Custodians shall validate protection requirements for information assets under their purview on an annual basis.
-
-
The department Information Asset Custodians:
-
In collaboration with the Owners of Information Assets shall define protection requirements for information assets under their purview.
-
Shall implement, manage, maintain, monitor, and periodically test physical and environmental protection controls to safeguard State information assets for which they have custodianship and as defined by the respective Owners of Information Assets.
-
Shall track and monitor all access to information assets, including physical access, as defined by Owners of Information Assets, and physical and environmental controls to validate correct operation.
-
Shall maintain all maintenance records and results of periodic tests.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the CDT OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
State Administrative Manual, Section 5325, Business Continuity Planning
-
State Administrative Manual, Section 5360, Identity and Access Management
-
State Administrative Manual, Section 5365, Physical Security
-
National Institute of Standards and Technology, Special Publications 800-53, Physical and Environmental Protection, PE-1, PE-2, PE-3, PE-4, PE-5, PE-6, PE-8, PE-9, PE-10, PE-11, PE-12, PE-13, PE-14, PE-15, PE-16, PE-17
-
National Institute of Standards and Technology, Special Publications 800-53, Maintenance, MA-1, MA-2, MA-3, MA-4, MA-5
-
National Institute of Standards and Technology, Special Publications 800-53, Contingency Planning, CP-2, CP-3
-
National Institute of Standards and Technology, Special Publications 800-53, Incident Response, IR-1, IR-2, IR-3, IR-4, IR-5, IR-6, IR-7
-
National Institute of Standards and Technology, Special Publications 800-53, Media Protection, MP-1, MP-2, MP-3, MP-4, MP-5, MP-6, MP-7
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 45, Section 49020.9, 49020.10
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 03/2022
-
5.3.18 Security Assessment and Authorization
-
Introduction and Overview
-
California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA) is responsible for the integration of information security and privacy within the organization. This includes, but is not limited to, the design and early identification of appropriate security controls in information asset acquisitions, in the design of new systems, or existing systems that are undergoing substantial redesign, including both in-house and outsourced solutions.
-
The CDCR, CCHCS, and CALPIA (hereinafter referred to as department) shall ensure its Information Security Officer (ISO) and, where applicable, its Privacy Program Coordinator and Technology Recovery Coordinator, are actively engaged with both the owners of information assets, and any relevant project, procurement, and technical personnel, to identify and implement the appropriate security controls required to manage risk to acceptable levels. Where applicable, the department ISO shall also work with other stakeholders, as appropriate.
-
-
Objectives
-
The objective for this policy is to establish a documented security assessment and authorization plan.
-
-
Scope and Applicability
-
The scope of this policy extends to all State and Agency information assets owned or operated by the department.
-
This policy applies to the department ISO, Privacy Officer, Privacy Program Coordinator, program management, Owners of Information Assets and Information Asset Custodians.
-
-
Policy Directives
-
The department shall ensure that a plan for assessing security controls in department information assets is defined and documented. The plan shall include the following:
-
Roles and responsibilities for security assessments and authorization.
-
Assessments are integrated in life cycle processes and operational assessments, and identify weaknesses and deficiencies early in information asset acquisition, development, and integration processes.
-
Essential information needed to make risk management decisions as part of security authorization processes is provided to the defined risk decision makers.
-
-
Roles and Responsibilities
-
The department Chief Information Officer (CIO) or Designee:
-
Owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
Is responsible for ensuring that this policy is reviewed annually, and updated accordingly.
-
Is required to audit and assess compliance with this policy at least once every two years.
-
-
The department Information Security Officer (ISO) shall facilitate security assessments and authorizations, and shall provide advice as appropriate.
-
The department Owners of Information Assets and Program Management in collaboration with Information Asset Custodians shall:
-
Ensure that this policy is implemented and shall review the policy’s implementation annually.
-
Ensure requisite security controls are implemented in accordance with applicable security requirements and documented authorizations for information assets.
-
Ensure that any security control gaps and residual risks being accepted are formally documented.
-
Ensure that records and results of assessments and risk decisions are maintained.
-
Ensure that records and results of assessments and risk decisions are provided to information security officers in a timely manner.
-
-
The department Information Asset Custodians shall implement the requisite security controls based upon the sensitivity or criticality of the assets as defined by the owners of information assets.
-
The department Privacy Officer/Privacy Program Coordinator shall ensure that privacy threshold and privacy impact assessments are completed as part of the security assessment and authorization process.
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards, and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, The department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the department ISO.
-
-
Authority
-
This policy complies with California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual, Section 5305-A, Information Security Program Management Standard
-
State Administrative Manual, Section 5305.7, Risk Assessment
-
State Administrative Manual, Section 5315, Information Security Integration
-
State Administrative Manual, Section 5315.9, Security Authorization
-
National Institute of Standards and Technology, Special Publications 800-53, Asset, Authorization, and Monitoring, (CA), CA-1, CA-2, CA-4, CA-6
-
National Institute of Standards and Technology, Special Publications 800-53, System and Information Integrity Policy and Procedures (SI), SI-1, SI 6, SI-12
-
National Institute of Standards and Technology, Special Publications 800-37, Risk Management Framework for Information Systems and Organizations: A Systems Life Cycle Approach for Security and Privacy
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 4, Article 45, Sections 49020.9
-
California Government Code, Section 11549.3
-
-
Revision History
-
Effective: 03/2022
-
5.3.19 Audit and Accountability
-
Introduction and Overview
-
In order to detect and respond to signs of attack, anomalies, and suspicious or inappropriate activities, California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA), hereinafter referred to as department, requires an audit and security event logging strategy to continuously monitor access and activities conducted using department information assets.
-
Information assets owned by the department are strategic assets intended for official business use, and are entrusted to state personnel and business partners in the performance of their job-related duties. Since inappropriate or unauthorized access and use of department information assets could result in harm to the state and to the department, it is important to detect and respond to signs of attack, anomalies, and suspicious or inappropriate activities in a timely and proper manner.
-
-
Objectives
-
This policy guides the development and implementation of department event logging and continuous monitoring strategy and supporting processes to identify and respond to indicators of attack, anomalies, and suspicious or inappropriate activities.
-
-
Scope and Applicability
-
The scope of this policy extends to all information assets owned or operated by the department.
-
This policy is applicable to department Owners of Information Assets and Information Asset Custodians.
-
-
Policy Directives
-
Department Owners of Information Assets in collaboration with Information Asset Custodians and the department Information Security Officer (ISO) shall develop and implement an event logging and continuous monitoring strategy of access and activities conducted using department information assets. This strategy shall include, at a minimum, the following items:
-
Define and document the audit logging requirements and security events that shall be recorded, monitored, and reviewed.
-
Identify and implement controls for audit trails and auditability of events for each system as well as for the internal network, accounting for segregation of duties, as appropriate.
-
Perform, at minimum, monthly monitoring of event logs of critical information assets to identify and respond to indicators of attacks, anomalies, and suspicious or inappropriate activities in a timely manner.
-
Define secure storage and retention of event logs.
-
Clearly define roles and responsibilities for event logging and monitoring.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee
-
The CIO or designee owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
The CIO or designee is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
The CIO or designee is required to audit and assess compliance with this policy at least once every two (2) years.
-
-
Department Information Security Officer (ISO)
-
The ISO shall guide the development and implementation of the department event logging and continuous monitoring strategy.
-
-
Department Owners of Information Assets and Program Management
-
Owners of Information Assets in collaboration with Information Asset Custodians are responsible for ensuring the protection of information assets under their purview.
-
Owners of Information Assets shall participate in the development and implementation of an event logging and continuous monitoring strategy.
-
Owners of Information Assets shall ensure assets are independently and continuously monitored based on the criticality of information assets.
-
-
Department Information Asset Custodians
-
Information Asset Custodians shall participate in the development and implementation of an event logging and continuous monitoring strategy.
-
Information Asset Custodians shall implement and maintain the department event logging and continuous monitoring strategy.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with state laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of state information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual 5305-A, Information Security Program Management Standard
-
Statewide Information Management Manual 5340-A, Incident Reporting and Response Instructions
-
State Administrative Manual, Section 5335, Information Security Monitoring
-
State Administrative Manual, Section 5335.1, Continuous Monitoring
-
State Administrative Manual, Section 5335.2, Auditable Events
-
National Institute of Standards and Technology Special Publications 800-53, Audit and Accountability, AU-1, AU-2, AU-3, AU-4, AU-5, AU-6, AU-7, AU-8, AU-9, AU-10, AU-11
-
National Institute of Standards and Technology Special Publications 800-53, Physical and Environmental Protection, PE-2, PE-6, PE-8
-
National Institute of Standards and Technology Special Publications 800-53, Risk Assessment, RA-3
-
California Department of Corrections and Rehabilitation, Department Operations Manual, Chapter 3, Article 22
-
California Government Code Section 11549.3
-
-
Revision History
-
Effective: 11/30/2022
-
5.3.20 Data Retention and Destruction
-
Introduction and Overview
-
The purpose of this policy is to ensure that necessary records and documents are adequately protected and maintained. Records that have reached the records retention maximum lifespan or that are no longer deemed necessary by the California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA), hereinafter referred to as department, are to be destroyed at the proper time and in a secure manner, consistent with records management policies outlined by the Secretary of State’s Office. The policy also describes the obligations of department employees to retain electronic and non‑electronic documents and their proper disposal.
-
-
Objectives
-
The objective of this policy is to establish the requirements for retaining or disposing of paper and electronic documents including but not limited to:
-
E-mails, texts, chats, and instant messages.
-
Video, audio, and image files.
-
Word processing and spreadsheet files.
-
Website activity and history.
-
Information posted on social networking websites.
-
Voice mails and video mail.
-
Computer programming information, system and audit logs, configuration details.
-
Physical paper documents, media and artifacts.
-
-
Scope and Applicability
-
The scope of this policy extends to all state information assets owned or operated by the department, as well as information assets owned and operated by third parties (if applicable) on behalf of the department.
-
This policy applies to the department’s Chief Information Officer (CIO) or designee, program management, Owners of Information Assets, Department Information Security Officers, Records Management Coordinators (RMC), Records Management Assistant Coordinators (RMAC), Technology Recovery Plan Coordinators, and Information Asset Custodians.
-
-
Policy Directives
-
Pursuant to California Government Code Sections 12270-12279, the department shall set records retention schedules to address legal, statutory, and compliance requirements as well as litigation needs, business processes, and data privacy concerns. Storage requirements shall be coordinated with the department RMC to ensure compliance with the State Records Management Act.
-
The department shall:
-
Ensure that roles and responsibilities for the identification, classification, and life cycle management of all department data and information assets are defined, documented, and implemented.
-
Ensure that all department information assets, including information and information systems, are categorized according to their criticality to department in accordance with SAM 5305.5, as well as to their sensitivity and susceptibility to inadvertent damage, loss or exposure and corresponding impacts to department.
-
Ensure that methods to protect the confidentiality, integrity, and availability of department data and information assets according to their classification are defined, documented, and implemented.
-
Ensure that conditions for access to and use of department information assets for all personnel are defined and documented.
-
Ensure that all personnel with access to department data and information assets are trained regarding data access and handling according to their roles and responsibilities.
-
Ensure that department data and information assets are used solely for their intended purpose.
-
Ensure that department data and information assets are securely destroyed and disposed of once they are no longer required by the department.
-
Ensure regular backups shall be completed based on department back-up and retention policy.
-
-
-
Data Retention Requirements
-
Retention procedures shall specify:
-
Steps used to archive information and locations where this information is stored.
-
The appropriate destruction of stored information, electronic or other format, after the identified retention period expires. Such steps shall adhere to the requirements outlined in this policy.
-
Chain of custody and handling of stored information, electronic or other format, when under litigation.
-
-
In certain instances, individual business units have unique record retention requirements outside of documented groups. These requirements shall be documented as part of internal processes and procedures and communicated to the Information Security Officer (ISO), RMC and RMAC. Such requirements may include contractual obligations with customers or business contacts or data retention requirements to maintain business operations. In some instances, departments may need to retain electronically stored information for a historical archive.
-
During the appropriate retention period for electronic records, archived data shall be retrievable. Doing so requires the following protocols:
-
As new software or hardware is implemented, appropriate department support staff shall ensure new systems and file formats can read legacy data. This may require that older data is converted to newer formats where possible.
-
Data that is encrypted shall be retrievable. The department shall implement key management procedures to ensure encrypted data can be decrypted when needed.
-
-
When establishing record retention periods, the department shall rely on (in order of precedence):
-
Federal and state laws and statutes and regulations.
-
State guidelines, recommendations, rules, and statutory requirements.
-
Internal department requirements and policies.
-
-
-
Audit Controls and Management
-
Documented procedures shall be in place for this policy and reviewed annually and updated as needed. Effective organizational management, audit controls, and employee practices include:
-
Documented record retention schedules and archival information of the department.
-
Procedures and anecdotal evidence of data migrations to manage electronic record compatibility with newer systems.
-
Documented encryption and decryption strategies that allow for retrieval of archival electronic records.
-
Employee procedures and documentation of records management and archival processes.
-
Direct observation of archival records organization and storage.
-
-
Expiration of Retention Period
-
Once a record or data has reached its designated retention period date, the Owner of Information Assets shall refer to the department Data Retention Schedule for appropriate action in accordance with the California State Records Management Act.
-
-
Sanitization and Destruction
-
When no longer usable, hard drives, diskettes, tape cartridges, CDs, ribbons, hard copies, print-outs, and other similar items used to process, store or transmit sensitive or confidential data shall be properly disposed of in accordance with measures established by SAM 5900 and 1600. (See NIST 800-88, Guidelines for Media Sanitization for further assistance.)
-
Physical media (paper print-outs and other physical media) shall be disposed of by one of the following methods:
-
Shredded using department issued cross-cut shredders.
-
Placed in locked shredding bins for third party shredding to come on-site, retrieve bins and securely shred.
-
-
Electronic/Magnetic media (hard drives, tape cartridges, CDs, printer ribbons, flash drives, printer and copier hard drives, smart devices, etc.) shall be disposed of by one of the following methods: (See NIST 800-88, Guidelines for Media Sanitization, Appendix A for further details.)
-
Clear – applies logical techniques to sanitize data in all user-addressable storage locations for protection against simple non-invasive data recovery techniques.
-
Purge – applies physical or logical techniques that render Target Data recovery infeasible.
-
Destroy – renders Target Data recovery infeasible and results in the subsequent inability to use the media for storage of data.
-
-
-
IT systems that have been used to process, store, or transmit sensitive or confidential information shall not be released from the department’s control until the equipment has been sanitized and all stored information has been cleared using one of the above methods.
-
-
Suspension of Record Disposal in Event of Litigation Hold
-
Preservation of data is a response to issues involving litigation, legislation, and requests for data pursuant to public records requests. The department shall comply with multiple federal and state laws, legal proceedings, state regulations and standards for the proper preservation and delivery of relevant physical and electronically stored information (ESI) in a timely and reliable manner. Legal counsel shall take such steps as necessary to promptly inform all staff of any suspension in the further disposal of documents. Please refer to the department eDiscovery and Litigation Hold Policy for further details.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee
-
The CIO or Designee owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
The CIO or Designee is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
The CIO or Designee is required to audit and assess compliance with this policy at least once every two (2) years.
-
-
Department Information Security Officer (ISO)
-
The ISO shall ensure processes exist for the secure destruction of paper and electronic records when no longer needed.
-
The ISO shall ensure specific retention requirements for sensitive or confidential data as defined by the Owners of Information Assets are adhered to.
-
The ISO shall ensure the safe and secure disposal of confidential data and information assets.
-
The ISO shall assist Owners of Information Assets and Information Asset Custodians in the identification of data security controls and processes.
-
-
Department Owners of Information Assets and Program Management
-
Owners of Information Assets shall ensure that no document is retained for longer than is legally or contractually allowed.
-
Owners of Information Assets shall implement data retention and disposal guidelines limiting data storage and retention times in accordance with legal, regulatory, and business requirements.
-
Owners of Information Assets shall define and enforce data retention requirements.
-
-
Department Information Asset Custodians
-
Information Asset Custodians shall assist Owners of Information Assets in identifying data retention security controls commensurate with the classification of the data.
-
Information Asset Custodians shall document, implement, monitor, and maintain data retention security protection controls as defined by Owners of Information Assets.
-
Information Asset Custodians shall develop and implement tools, technologies, processes, and procedures to support, monitor and maintain data retention security controls.
-
-
Department Records Management Coordinator (RMC) and Records Management Assistant Coordinator (RMAC)
-
The RMC, pursuant to Gov. Code 12274, shall assist the RMACs, Owners and Custodians of Information Assets in establishing proper data retention periods.
-
The RMC shall assist in training identified RMACs and entity staff in records retention.
-
The RMACs shall ensure that required data retention periods are maintained and data beyond the lifecycle of established policy is properly disposed.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, Information Security Officer (ISO), and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with state laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of state information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
State Administrative Manual, Section 5305.5, Information Asset Management
-
State Administrative Manual, Section 5310.4, Individual Access to Personal Information
-
State Administrative Manual, Section 5310.6, Data Retention and Destruction
-
State Administrative Manual, Section 5310.7, Security safeguards
-
State Administrative Manual, Section 5340, Information Security Incident Management
-
State Administrative Manual, Section 5340.1, Incident Response Training
-
State Administrative Manual, Section 5340.2, Incident Response Testing
-
State Administrative Manual, Section 5340.3, Incident Handling
-
State Administrative Manual, Section 5340.4, Incident Reporting
-
State Administrative Manual, Section 5350, Encryption
-
State Administrative Manual, Section 5365, Physical access
-
State Administrative Manual, Section 5365.1, Access Control for Output Devices
-
State Administrative Manual, Section 5365.2, Media Protection
-
State Administrative Manual, Section 5365.3, Media Disposal
-
Federal Information Processing Standard, FIPS 199
-
National Institute of Standards and Technology Special Publications 800-53, Access Control, AC-3, AC-4
-
National Institute of Standards and Technology Special Publications 800-53, Audit and Accountability, AU-2, AU-3, AU-13
-
National Institute of Standards and Technology Special Publications 800-53, Configuration Management, CM-8
-
National Institute of Standards and Technology Special Publications 800-53, Media Protection, MP-1, MP-2, MP-3, MP-4, MP-5, MP-6, MP-7
-
National Institute of Standards and Technology Special Publications 800-53, Physical and Environmental Protection, PE-5, PE-19, PE-20
-
National Institute of Standards and Technology Special Publications 800-53, Planning, PL-4
-
National Institute of Standards and Technology Special Publications 800-53, Program Management, PM-9
-
National Institute of Standards and Technology Special Publications 800-53, Risk Assessment, RA-2, RA-3
-
National Institute of Standards and Technology Special Publications 800-53, Security Assessment and Authorization, CA-7
-
National Institute of Standards and Technology Special Publications 800-53, System and Communications Protection, SC-4, SC-8, SC-13, SC‑17, SC-28
-
National Institute of Standards and Technology Special Publications 800-53, System and Services Acquisition, SA-11
-
National Institute of Standards and Technology Special Publications 800-53, System and Information Integrity, SI-12
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 1, Article 23, Sections 14060.6.5, 14060.6.6
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 38, Section 47110.15
-
California Government Code Section 11549.3
-
-
Revision History
-
Effective: 11/30/2022
-
5.3.21 Data Security
-
Introduction and Overview
-
California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA), hereinafter referred to as department, collects, processes, transmits, and stores large amounts of data to support essential missions and business functions. Some data maintained by the department may be sensitive or confidential, and may require special precautions to protect it from unauthorized modification, or deletion as per the State Administrative Manual.
-
The department has the responsibility to classify its data and information assets, and to implement suitable controls to protect it from unauthorized access, corruption, or loss.
-
-
Objectives
-
The primary objective for this policy is to define department requirements to manage the confidentiality, integrity, and availability of department data and information assets throughout their lifecycles: from collection, creation, storage, and use, to destruction and disposal.
-
-
Scope and Applicability
-
The scope of this policy extends to all state and agency data and information assets owned or operated by the department, and operated by third parties on behalf of the department, and governs all state and department data and information assets in all forms and media types, including digital and physical formats.
-
This policy applies to all department personnel.
-
-
Policy Directives
-
The department shall:
-
Ensure that roles and responsibilities for the identification, classification, and life cycle management of all department data and information assets are defined, documented, and implemented.
-
Ensure that all department information assets, including information and information systems, are categorized according to their criticality, as well as their sensitivity and susceptibility to inadvertent damage, loss, or exposure and corresponding impact to the department.
-
Ensure that methods to protect the confidentiality, integrity, and availability of department data and information assets according to their classification are defined, documented, and implemented.
-
Ensure that conditions for access to and use of department information assets for all personnel are defined and documented.
-
Ensure that all personnel with access to department data and information assets are trained regarding data access and handling according to their roles and responsibilities.
-
Ensure that department data and information assets are used solely for their intended purpose.
-
Ensure that department data and information assets are securely destroyed and disposed of once they are no longer required by the department.
-
Ensure that the proper authorities are notified of data security incidents as required.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee
-
The CIO or designee owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
The CIO or designee is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
The CIO or designee is required to audit and assess compliance with this policy at least once every two years.
-
-
Department Information Security Officer (ISO)
-
The ISO shall assist Owners of Information Assets and Information Asset Custodians in the identification of data security controls and processes.
-
The ISO shall participate in incidents involving data security.
-
The ISO shall ensure that data security controls, methods and processes meet department and applicable regulatory requirements for security and privacy.
-
-
Department Owners of Information Assets and Program Management
-
Owners of Information Assets shall ensure that this policy is implemented and reviewed annually, and updated as necessary.
-
Owners of Information Assets shall ensure that roles and responsibilities for the identification, classification, and life cycle management of all data and information assets under their purview are defined, documented and implemented.
-
Owners of Information Assets shall ensure confidentiality and integrity controls commensurate with asset classification are implemented for data and information assets under their purview.
-
Owners of Information Assets shall ensure that conditions and rules for access, availability, and use of data and information assets under their purview are commensurate with asset classification.
-
-
Department Information Asset Custodians
-
Information Asset Custodians shall assist Owners of Information Assets in identifying data security controls commensurate with the classification of the data.
-
Information Asset Custodians shall document, implement, monitor, and maintain data security protection controls as defined by Owners of Information Assets.
-
Information Asset Custodians shall develop and implement tools, technologies, processes, and procedures to support, monitor and maintain data security controls.
-
Information Asset Custodians shall notify respective Owners of Information Assets and the department Information Security Officer (ISO) and the Privacy Officer of all security incidents pertaining to the security of department data, particularly if the incident is related to personally identifiable information (PII).
-
Information Asset Custodians shall maintain data security records as defined by Owners of Information Assets commensurate with the classification of the data.
-
-
Department Users
-
Users of department information assets shall be aware of and adhere to all department information security and privacy policies.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with state laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of state information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual 5305-A, Information Security Program Management Standard
-
State Administrative Manual, Section 5305.5, Information Asset Management
-
State Administrative Manual, Section 5310.4, Individual Access to Personal Information
-
State Administrative Manual, Section 5310.6, Data Retention and Destruction
-
State Administrative Manual, Section 5310.7, Security safeguards
-
State Administrative Manual, Section 5340, Information Security Incident Management
-
State Administrative Manual, Section 5340.1, Incident Response Training
-
State Administrative Manual, Section 5340.2, Incident Response Testing
-
State Administrative Manual, Section 5340.3, Incident Handling
-
State Administrative Manual, Section 5340.4, Incident Reporting
-
State Administrative Manual, Section 5350, Encryption
-
State Administrative Manual, Section 5365, Physical access
-
State Administrative Manual, Section 5365.1, Access Control for Output Devices
-
State Administrative Manual, Section 5365.2, Media Protection
-
State Administrative Manual, Section 5365.3, Media Disposal
-
Federal Information Processing Standard, FIPS 199
-
National Institute of Standards and Technology, Special Publications 800-53, Access Control, AC-3, AC-4
-
National Institute of Standards and Technology, Special Publications 800-53, Audit and Accountability, AU-2, AU-3, AU-13
-
National Institute of Standards and Technology, Special Publications 800-53, Configuration Management, CM-8
-
National Institute of Standards and Technology, Special Publications 800-53, Media Protection, MP-1, MP-2, MP-3, MP-4, MP-5, MP-6, MP-7
-
National Institute of Standards and Technology, Special Publications 800-53, Physical and Environmental Protection, PE-5, PE-19, PE-20
-
National Institute of Standards and Technology, Special Publications 800-53, Planning, PL-4
-
National Institute of Standards and Technology, Special Publications 800-53, Program Management, PM-9
-
National Institute of Standards and Technology, Special Publications 800-53, Risk Assessment, RA-2, RA-3
-
National Institute of Standards and Technology, Special Publications 800-53, Security Assessment and Authorization, CA-7
-
National Institute of Standards and Technology, Special Publications 800-53, System and Communications Protection, SC-4, SC-8, SC-13, SC-17, SC-28
-
National Institute of Standards and Technology, Special Publications 800-53, System and Services Acquisition, SA-11
-
National Institute of Standards and Technology, Special Publications 800-53, System and Information Integrity, SI-12
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 45, Section 49020.6, 49020.6.1, 49020.6.2
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 46, Section 49030.4
-
California Government Code Section 11549.3
-
-
Revision History
-
Effective: 11/30/2022
-
5.3.22 eDiscovery and Litigation Hold
-
Introduction and Overview
-
Preserving data is necessary in response to reasonably foreseeable litigation, subpoenas, or Public Records Act (PRA) requests, and may be required under applicable state and federal laws and regulations. Data may include both physical and electronically stored information (ESI). ESI is broadly defined as any information stored in an electronic medium, regardless of its manner of creation or use.
-
-
Objectives
-
The objective of this policy is to establish California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA), hereinafter referred to as department, requirements for identification, preservation, capture, and delivery of relevant data in response to requests for information, audit, archive, and legal proceedings.
-
-
Scope and Applicability
-
The scope of this policy extends to all information assets owned or operated by the department, as well as information assets owned or operated by third parties (if applicable) on behalf of the department.
-
This policy applies to the department’s Chief Information Officer (CIO) or their designee, data owners, legal compliance staff, Agency and Department Information Security Officers, Privacy Officers, Privacy Program Coordinators, Records Management Coordinator (RMC), Records Management Assistant Coordinators (RMACs), Information Asset Custodians, and all users of department information systems.
-
-
Policy Directives
-
The department shall:
-
Preserve specific active and archived stored information and follow department data classification procedures when a litigation hold request is made.
-
Provide a written litigation hold notice to all involved parties with clear instructions on what should be preserved and held.
-
Ensure data and metadata are stored in a manner such that the data source is known and secured.
-
Ensure necessary and appropriate record retention systems are created and maintained consistent with the records management policies outlined by the Secretary of State’s Office.
-
Ensure proper controls for the preservation of data are implemented, including electronic communications which may reasonably be subject to legal proceedings.
-
Establish a process for the intake and fulfillment of PRA requests.
-
Establish standard protocols for the collection, analysis, and delivery of data including chain of custody, data integrity and auditability of records.
-
Provide Records Retention and eDiscovery training to appropriate staff.
-
Return or destroy all preserved or archived data to the affected individuals and resume the normal destruction schedule after the legal duty to preserve evidence ends.
-
-
Electronically Stored Information Subject to Discovery
-
ESI is any information stored in an electronic medium, regardless of its format, location, or medium. ESI is subject to discovery in civil litigation and may also be requested under the PRA. ESI includes, but is not limited to:
-
E-mails, texts, chats, and instant messages.
-
Video, audio, and image files.
-
Word processing and spreadsheet files.
-
Website activity and history.
-
Information posted on social networking websites.
-
Voice mails and video mail.
-
Computer programming information, system and audit logs, configuration details.
-
-
In the event of a litigation hold, this policy shall supersede requirements set forth in the Data Retention and Destruction Policy.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee
-
The CIO or designee owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
The CIO or designee is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
The CIO or designee is required to audit and assess compliance with this policy at least once every two years.
-
The CIO or designee is responsible for establishing eDiscovery teams in order to efficiently and properly coordinate the responses to PRA requests and information, audit, archive and legal proceedings.
-
-
Department Information Security Officer (ISO)
-
The ISO is responsible for the oversight of all department data preservation and compliance requirements and ensures that all applicable standards and guidelines are maintained and reviewed regularly.
-
The ISO shall assist in the development of data preservation, planning, and production of entity data assets.
-
The ISO shall assist the RMC, RMACs, Owners of Information Assets, and Information Asset Custodians with ensuring that data preservation, storage, integrity, and delivery meet the SAM 5310, 5310.5, 5310.6 and SAM 5305 requirements for security and privacy.
-
-
Department Owners of Information Assets and Program Management
-
Owners of Information Assets and program management supporting the department mission, state essential functions, or critical infrastructure shall participate in records retention processes, and ensure data is classified, labeled, and managed according to defined standards.
-
Owners of Information Assets supporting the department mission, state essential functions, or critical infrastructure shall ensure that records management is incorporated into standard business operation practices.
-
Owners of Information Assets shall ensure that all pertinent data that is required for the eDiscovery process is preserved and maintained according to the department’s defined standards.
-
-
Department Information Asset Custodians
-
Information Asset Custodians shall only assist with authorized data collection and preservation requests.
-
Information Asset Custodians shall ensure that the integrity of the data collection and preservation process is maintained and the request is fulfilled.
-
Information Asset Custodians shall ensure the requested data is secure and available to the legal team as needed.
-
-
Department Legal Counsel
-
Legal Counsel shall provide the department eDiscovery designee a written notice to suspend routine or intentional purging of relevant data including overwriting, reusing, deleting, or any other destruction of electronic relevant information.
-
Legal Counsel shall notify appropriate parties when the obligation to retain the preserved data ends.
-
-
Department Records Management Coordinator (RMC) and Records Management Assistant Coordinator
-
The RMC, pursuant to Gov. Code 12274, shall assist the RMACs, Owners, and Custodians of Information Assets in establishing appropriate data retention periods.
-
The RMC shall assist in training identified RMACs and entity staff in records retention.
-
The RMACs shall ensure that required data retention periods are maintained and data beyond the lifecycle of established policy is properly disposed.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with state laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of state information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual, Section 5305-A, Data Retention and Destruction
-
State Administrative Manual, Section 5010, Maintenance Records
-
State Administrative Manual, Section 1600, Records Management
-
State Administrative Manual, Section 5310.6, Data Retention and Destruction
-
Federal Information Processing Standard, FIPS 199
-
National Institute of Standards and Technology, Special Publications 800-53, Access Control, AC-3, AC-4
-
National Institute of Standards and Technology, Special Publications 800-53, Audit and Accountability, AU-2, AU-3, AU-13
-
National Institute of Standards and Technology, Special Publications 800-53, Configuration Management, CM-8
-
National Institute of Standards and Technology, Special Publications 800-53, Media Protection, MP-1, MP-2, MP-3, MP-4, MP-5, MP-6, MP-7
-
National Institute of Standards and Technology, Special Publications 800-53, Physical and Environmental Protection, PE-5, PE-19, PE-20
-
National Institute of Standards and Technology, Special Publications 800-53, Planning, PL-4
-
National Institute of Standards and Technology, Special Publications 800-53, Program Management, PM-9
-
National Institute of Standards and Technology, Special Publications 800-53, Risk Assessment, RA-2, RA-3
-
National Institute of Standards and Technology, Special Publications 800-53, Security Assessment and Authorization, CA-7
-
National Institute of Standards and Technology, Special Publications 800-53, System and Communications Protection, SC-4, SC-8, SC-13, SC 17, SC-28
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 1, Article 16, Sections 13040.7, 13040.7.1, 13040.7.2
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 36, Section 47090.10
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 38, Sections 47110.7, 47110.16
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 45, Section 49020.10.6
-
California Government Code Section 6250
-
California Government Code Section 11549.3
-
-
Revision History
-
Effective: 11/30/2022
-
5.3.22.1 Health Care Litigation Support eDiscovery and Litigation Hold
-
Policy
-
California Correctional Health Care Services (CCHCS) shall protect and preserve electronically stored information (ESI) under health care (medical, mental health, and dental) for litigation and California Public Records Act (PRA) purposes. ESI is discoverable under the California Code of Civil Procedure, Sections 2031.010(a), (e) and 2031.030(a)(2), (c)(1). No data will be disclosed without first being reviewed by the Health Care Litigation Support Section (LSS) and, when needed, CCHCS’ Office of Legal Affairs (COLA) to ensure legal necessity, relevance, and removal of all privileged information.
-
-
Responsibilities
-
The Deputy Director, Policy and Risk Management Services, or designee, has the authority to coordinate the protection and preservation of ESI, release records requested for litigation, investigation, and PRA purposes and shall ensure departmental compliance with this policy.
-
The Associate Director (AD), Risk Management Branch (RMB), shall designate a CCHCS Litigation Coordinator and CCHCS PRA Coordinator, or designee, responsible for coordinating the preservation, retention, discovery, and response to all health care-related litigation and PRA requests.
-
LSS is responsible for coordinating the preservation, retention, discovery, and production of ESI relevant to health care-related litigation and PRA requests.
-
-
Procedure
-
Litigation Hold
-
Litigation holds may be placed on ESI including, but not limited to, health records; health care grievances; emails; text messages; voice mail messages; video, audio, and image files; website activity and history; hard drives; state-issued cell phone data; and personnel records for which CCHCS is the custodian of records.
-
LSS staff shall:
-
Preserve or retain ESI as required when a request or retention letter is received from the Office of Attorney General (OAG), CDCR Office of Legal Affairs (OLA), COLA, contract counsel, or private law office.
-
Conduct preservation or retention in the manner, timeframe and for the specific active and archived ESI as required in the letter of preservation or retention.
-
Follow department data classification procedures when a litigation hold request is made, and if requested, provide a written litigation hold notice to all involved parties with clear instructions on what should be preserved and held.
-
Ensure proper controls for the preservation of ESI are implemented, as it may be subject to legal proceedings.
-
-
Litigation holds shall be released upon closure of a lawsuit or dismissal of a defendant.
-
-
eDiscovery for Litigation
-
The eDiscovery process, which includes identifying, obtaining, and exchanging ESI, shall only be used for litigation or investigational purposes to ensure the security of sensitive or pertinent information.
-
To fulfill litigation or investigation obligations, LSS shall utilize eDiscovery software to:
-
Conduct email searches.
-
Facilitate access to eDiscovery software for the OAG, OLA, COLA.
-
Coordinate with CCHCS and CDCR staff on eDiscovery efforts.
-
Manage necessary storage and production in consultation with the Information Technology Services Division as directed by the OAG, OLA, COLA, or contract counsel.
-
-
-
eDiscovery for Public Records Act Requests
-
Any member of the public may request email records pursuant to California Government Code, Sections 7920.000-7930.215.
-
LSS staff shall conduct an eDiscovery search within parameters responsive to the request.
-
Additional information related to PRA requests is outlined in the Health Care Department Operations Manual, Section 5.1.2, California Public Records Act Requests.
-
-
-
Training and Resources
-
LSS staff shall utilize the Health Care Litigation Support Section Operating Standards and resource documents available on the CCHCS Intranet.
-
LSS shall provide Records Retention and eDiscovery training to appropriate staff.
-
-
References
-
California Code of Civil Procedure, Part 4, Title 4, Chapter 14, Article 1, Section 2031.010(a), (e) and Section 2031.030(a)(2), (c)(1)
-
California Government Code Title 1, Division 10, Chapter 3.5 Inspection of Public Records, Sections 7920.000-7930.215
-
Health Care Department Operations Manual, Chapter 5, Article 1, Section 5.1.2, California Public Records Act Requests
-
-
Revision History
-
Effective: 08/02/2023
-
5.3.23 Identification and Authentication
-
Introduction and Overview
-
Information assets owned by California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA), hereinafter referred to as department, are intended to be accessed by authorized entities and used exclusively for department business purposes. Consequently, it is imperative that all entities requesting access to department information assets are uniquely identified prior to being granted access.
-
-
Objectives
-
The objective for this policy is to establish department requirements to control access to information assets by uniquely identifying the entities requesting access before access is granted.
-
-
Scope and Applicability
-
The scope of this policy extends to all state and agency information assets owned and operated by the department, information assets managed by third parties on behalf of the department, and all information assets that process or store department information in support of department services and mission.
-
This policy applies to all department personnel and processes acting on behalf of the department.
-
This policy governs physical and logical access. Logical access includes local access and network, including remote access.
-
-
Policy Directives
-
The department shall ensure that a department identity and access management (IAM) strategy is developed, clearly defined, documented, and implemented.
-
The department IAM strategy shall include the following:
-
Requirements to meet all state and federal requirements.
-
The unique identification of all authorized personnel or processes acting on behalf of the department that access department information assets prior to being granted access.
-
The use of appropriate credentials for the identification of non-state personnel.
-
Implement methods that enable non-repudiation of access requests to information assets containing sensitive and confidential data, and protect related audit logs for a period of no less than six months.
-
Implementation of a suitable IAM infrastructure supporting department requirements.
-
Implementation of safeguards to protect the confidentiality, integrity, and availability of the supporting IAM infrastructure.
-
Definition and implementation of authentication mechanisms based on the type and method of access and the inherent risks associated with each access use case.
-
Control and management of access by administrative and privileged users, including the ability to immediately revoke access when necessary.
-
Requirement to implement application level identification and authentication in addition to platform level access to provide additional security, as appropriate by Owners of Information Assets.
-
Definition, documentation, and implementation of audit and security activity and event logging requirements for privileged use.
-
Identification, development, and implementation of supporting identity and access management processes and procedures.
-
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee
-
The CIO or designee owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
The CIO or designee is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
The CIO or designee is required to audit and assess compliance with this policy at least once every two years.
-
-
Department Owners of Information Assets and Program Management
-
Owners of Information Assets shall ensure that this policy is implemented and shall review the policy’s implementation annually.
-
Owners of Information Assets in collaboration with Information Asset Custodians shall ensure that identification and authentication technologies and process controls commensurate with the sensitivity or criticality of the asset are implemented for assets under their purview.
-
-
Department Information Asset Custodians
-
Information Asset Custodians shall assist Owners of Information Assets in selecting and implementing identification and authentication technologies and process controls commensurate with the sensitivity or criticality of the asset.
-
Information Asset Custodians shall maintain the identification and authentication infrastructure and supporting processes and procedures.
-
Information Asset Custodians shall maintain identification and authentication records as defined by Owners of Information Assets for a minimum of twelve (12) months, or as defined by the department’s Information Security Officer (ISO).
-
-
Department Users
-
Users shall report any incidents of possible misuse or violation of this policy to the department ISO, designee, appropriate security staff or their immediate supervisor.
-
Users shall be aware of and adhere to all department information security and privacy policies.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with State laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of State information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual 5340-A, Incident Reporting and Response Instructions
-
Statewide Information Management Manual 5360-A, Telework and Remote Access Security Standard
-
State Administrative Manual, Section 5335, Information Security Monitoring
-
State Administrative Manual, Section 5340, Information Security Incident Management
-
State Administrative Manual, Section 5360, Identity and Access Management
-
National Institute of Standards and Technology, Special Publications 800-53, Identification and Authentication, IA-1, IA-2, IA-3, IA-4, IA-5, IA-6, IA 7, IA-8, IA-9, IA-10, IA-11, IA-12
-
National Institute of Standards and Technology, Special Publications 800-53, Access Control, AC-1, AC-2, AC-3, AC-4, AC-5, AC-5, AC-7, AC-8, AC 9, AC-10, AC-11, AC-12, AC-13, AC-14, AC-15, AC-16, AC-17, AC-18, AC-19, AC 20, AC-21, AC-22, AC-23, AC-24, AC-25
-
National Institute of Standards and Technology, Special Publications 800-53, Audit and Accountability, AU-1, AU-2, AU-10, AU-11, AU-12, AU-13
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 45, Sections 49020.5, 49020.10
-
California Government Code Section 11549.3
-
-
Revision History
-
Effective: 11/30/2022
-
5.3.24 Incident Response
-
Introduction and Overview
-
California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA), hereinafter referred to as department, management shall promptly investigate incidents involving loss, damage, misuse of information assets, or improper dissemination of information. Incidents could also include unauthorized access of information asset and incidents negatively affecting the operation, confidentiality, integrity, or availability of information assets. All entities are required to report information security incidents in accordance with the state information security notification and reporting requirements.
-
Effective incident management includes the formulation, adoption, and maintenance of a written incident management plan that provides for the timely assembly of appropriate staff that are capable of developing a response to, appropriate reporting about, and successful recovery from a variety of incidents. A defined and documented security incident response plan shall enable the department to detect, respond, and recover from security incidents in a timely and organized manner so as to minimize the impacts of the security incident.
-
-
Objectives
-
The objective for this policy is to establish the requirements for a department security incident response plan.
-
-
Scope and Applicability
-
The scope of this policy extends to all state and agency information assets owned or operated by the department as well as information assets managed by third parties on behalf of the department.
-
This policy applies to all department personnel.
-
-
Policy Directives
-
The department shall:
-
Ensure that a security incident response plan and related procedures, including specific responses to incidents involving Personally Identifiable Information (PII) are defined, documented and implemented.
-
Ensure that the security incident response plan and procedures clearly define and document roles and responsibilities to address the full incident life cycle, including:
-
Security incident detection and identification
-
Security incident response management
-
Incident handling team(s), with broad participation from other department stakeholders, under the coordination of a designated incident manager.
-
Preservation of evidence, including tracking and maintaining the evidence pertaining to chains of custody and evidence.
-
-
Ensure that mechanisms and procedures are implemented to enable personnel to report security incidents to the appropriate security staff and the department’s Office of Information Security. Ensure all department personnel are aware of incident reporting mechanisms and procedures.
-
Immediately report incidents through the California Compliance and Security Incident Reporting System (Cal-CSIRS) providing the incidents meet the reporting requirements. Cal-CSIRS requires specific details about the incident and shall notify the California Department of Technology Office of Information Security (OIS), as well as the California Highway Patrol (CHP) Computer Crimes Investigation Unit.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or designee
-
The CIO or designee owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
The CIO or designee shall ensure that the department has a formally documented and operational incident response plan to address incidents involving the loss, damage, misuse or unauthorized access of information assets, and breaches of security involving personal information in any form, in the most expedient and effective manner.
-
The CIO or designee shall ensure that the security incident response plan and procedures describe the necessary roles and responsibilities, and activities to enable security incident handlers to effectively prepare for, detect, analyze, contain, eradicate and recover from security incidents.
-
The CIO or designee shall ensure that security incident response management is integrated across the department, and with other state and department contingency and emergency management plans, teams and advisory resources.
-
The CIO or designee shall ensure that all department personnel receive incident response and awareness training and education in accordance with the individual’s functional role within the department.
-
The CIO or designee shall ensure that department incident response capabilities are exercised at least annually to test incident response effectiveness, and that results from tests are documented and reviewed to continuously improve capabilities.
-
The CIO or designee shall ensure that post-mortem/lessons-learned sessions following security incident response activities and tests are completed in order to continually improve incident response capabilities.
-
The CIO or designee shall ensure that all security incidents and department responses are monitored and documented, and all related activities and decisions are recorded.
-
The CIO or designee shall ensure that the department incident response plan, procedures and supporting documentation are updated at minimum on an annual basis.
-
The CIO or designee is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
The CIO or designee is required to audit and assess compliance with this policy at least once every two years.
-
-
Department Information Security Officer (ISO)
-
The ISO shall assist Owners of Information Assets and Information Asset Custodians in the development of department incident response plans.
-
The ISO shall participate in incident response and management activities.
-
-
Department Owners of Information Assets and Program Management.
-
Owners of Information Assets shall participate and provide assistance with and decisions related to responding to incidents involving information assets under their purview, as required, and as requested by incident managers, the Chief Information Officer (CIO) or Designee and the department ISO.
-
-
Department Information Asset Custodians
-
Information Asset Custodians shall participate and provide assistance with incident response activities as directed and guided by incident managers, ISOs, and Owners of Information Assets, as appropriate.
-
Information Asset Custodians shall maintain records related to and supporting individual incident responses.
-
-
Department Users
-
Users shall be aware of and adhere to all department information security and privacy policies.
-
Users shall report any incidents of possible misuse or violation of this policy to the department ISO, designee, or appropriate security staff or their immediate supervisor.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with state laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of state information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual 5340-A, Incident Reporting and Response Instructions
-
Statewide Information Management Manual 5340-B, Information Security Incident Report (Cal-CSIRS)
-
Statewide Information Management Manual 5340-C, Requirements to Respond to Incidents Involving a Breach of Personal Information
-
State Administrative Manual, Section 5340, Information Security Incident Management
-
State Administrative Manual, Section 5340.1, Incident Response Training
-
State Administrative Manual, Section 5340.2, Incident Response Testing
-
State Administrative Manual, Section 5340.3, Incident Handling
-
State Administrative Manual, Section 5340.4, Incident Reporting
-
National Institute of Standards and Technology, Special Publications 800-53, Contingency Planning, CP-2, CP-9, CP-10, CP-13
-
National Institute of Standards and Technology, Special Publications 800-53, Incident Response, IR-1, IR-2, IR-3, IR-4, IR-5, IR-6, IR-7, IR-8, IR 9, IR-10
-
National Institute of Standards and Technology, Special Publications 800-53, Program Management, PM-9
-
National Institute of Standards and Technology, Special Publications 800-53, Risk Assessment, RA-2, RA-3
-
National Institute of Standards and Technology, Special Publications 800-53, Security Assessment and Authorization, CA-7
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 45, 49020.12, 49020.12.1, 49020.12.2
-
California Government Code Section 11549.3
-
-
Revision History
-
Effective: 11/30/2022
-
5.3.25 Security and Privacy Awareness Training
-
Introduction and Overview
-
A well-trained workforce, aware of information privacy and security risk, plays a crucial role in protecting organizations against a variety of information security threats. Consequently, a formal privacy and security awareness training program is a key component of California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA)’s, hereinafter referred to as department, information security program.
-
-
Objectives
-
Objectives for this policy are to establish the requirement of a formal and effective department privacy and security awareness and training program for all department personnel.
-
-
Scope and Applicability
-
The scope of this policy applies to all department personnel and governs all forms of access to department information assets.
-
-
Policy Directives
-
The department shall:
-
Establish a formal department privacy and security awareness training program, with clearly defined roles and responsibilities, designed to be delivered to all personnel with access to department information assets.
-
Provide privacy and security awareness training to all personnel upon commencement of their employment with the department, and on an annual basis thereafter.
-
Ensure role-based privacy and security awareness training content is delivered commensurate with personnel roles and responsibilities.
-
Ensure effectiveness of the security awareness program through a process of tracking and reporting metrics.
-
Maintain individual records of all security and privacy training undertaken annually by department personnel for a period of three years or as defined in the records retention schedule.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee
-
The CIO or designee owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and their individual responsibilities.
-
The CIO or designee is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
The CIO or designee is required to audit and assess compliance with this policy at least once every two years.
-
-
Department Information Security Officer (ISO)
-
The ISO shall ensure the development implementation, and compliance of the department’s security awareness training program.
-
-
Department Privacy Officer
-
The Privacy Officer shall ensure the development, implementation, and compliance of the department’s privacy awareness training program.
-
-
Department Users
-
Users shall participate in all required privacy and security awareness training annually.
-
Users shall be aware of and adhere to all department information security and privacy policies.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the Department Operations Manual Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with state laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of state information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
The department Information Security Officer (ISO), Chief Privacy Officer or Coordinator and Training Coordinator shall provide department program management with regular reports on personnel participation in, and the effectiveness of privacy and security and awareness training.
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
State Administrative Manual, Section 5305.3, Information Security Roles and Responsibilities
-
State Administrative Manual, Section 5320, Training and Awareness for Security and Privacy
-
State Administrative Manual, Section 5320.1, Security and Privacy Awareness
-
State Administrative Manual, Section 5320.2, Security and Privacy Training
-
State Administrative Manual, Section 5320.3, Security and Privacy Training Records
-
State Administrative Manual, Section 5320.4, Personnel Security
-
National Institute of Standards and Technology, Special Publications 800-53, Planning, PL-4
-
National Institute of Standards and Technology, Special Publications 800-53, Awareness and Training, AT-1, AT-2, AT-3, AT-04
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 41, Section 48010.5
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 45, Sections 49020.4, 49020.7.2, 49020.7.3, 49020.7.3.1
-
California Government Code Section 11549.3
-
-
Revision History
-
Effective: 11/30/2022
-
5.3.26 Software Management and Licensing
-
Introduction and Overview
-
State entities are required to establish and maintain an inventory of all information assets, including information systems, information system components, software, and information repositories (both electronic and paper). The inventory shall contain a listing of all programs and information systems identified as processing, storing, or transmitting California Department of Corrections and Rehabilitation (CDCR), California Correctional Health Care Services (CCHCS), and California Prison Industry Authority (CALPIA), hereinafter referred to as department, information.
-
The department uses computer software applications that are owned by the state, as well as commercial software and open-source software (OSS) licensed for use from vendors.
-
This policy identifies department requirements for the management of department software assets.
-
-
Objectives
-
The objective of this policy is to establish formalized control and management of all types of software including the development of requisite tools, processes procedures and standards.
-
-
Scope and Applicability
-
The scope of this policy extends to all state and agency software assets owned or licensed by the department.
-
This policy applies to the department Information Security Officer, Program Management, Owners of Information Assets, and Information Asset Custodians.
-
-
Policy Directives
-
The department shall:
-
Maintain a detailed inventory of all approved department state-owned, commercial and open-source software, including licensing requirement(s), currency, and the cost of the software.
-
Control and manage all instances and usage of approved department software installed on department information assets in order to comply with all applicable legal, copyright, and licensing requirements.
-
Establish a continuous monitoring process to identify, detect, and remove all unapproved department software installed or operating on department information assets.
-
Develop, implement, and maintain a software management plan.
-
Identify and track any department software that is at end-of-support /end-of-life, and shall ensure that maintenance agreements and processes are in place where appropriate to ensure software can remain operational to meet business requirements.
-
Establish and maintain controls to prevent unauthorized personnel from installing software applications on state information assets.
-
-
Roles and Responsibilities
-
Department Chief Information Officer (CIO) or Designee
-
The CIO or designee owns this policy and is responsible for ensuring that all users of department information assets are aware of this policy and acknowledge their individual responsibilities.
-
The CIO or designee is responsible for ensuring that this policy is reviewed annually and updated accordingly.
-
The CIO or designee is required to audit and assess compliance with this policy at least once every two years.
-
-
Department Information Security Officer (ISO)
-
The ISO shall assist and provide advice in the evaluation and selection of department software.
-
The ISO shall assist and provide advice in the identification of security requirements that software shall comply with.
-
-
Department Owners of Information Assets and Program Management
-
Owners of Information Assets shall ensure that this policy is implemented and shall review the policy’s implementation annually.
-
Owners of Information Assets shall ensure that software assets under their purview are controlled and managed.
-
-
Department Information Asset Custodians
-
Information Asset Custodians shall implement software management, licensing, and usage controls as approved by Owners of Information Assets.
-
Information Asset Custodians shall maintain all department software licenses associated with commercial products on behalf of Owners of Information Assets.
-
-
-
Enforcement
-
Non-compliance with this policy may result in disciplinary or adverse action as set forth in the Department Operations Manual, Chapter 3, Article 22.
-
The department shall comply with the information security and privacy policies, standards and procedures issued by the California Department of Technology (CDT), Office of Information Security (OIS). In addition to compliance with the information security and privacy policies, standards, procedures, and filing requirements issued by the OIS, the department shall ensure compliance with all security and privacy laws, regulations, rules, and standards specific to and governing the administration of their programs. Program administrators shall work with their general counsel, ISO, and Privacy Program Officer or Coordinator to identify all security and privacy requirements applicable to their programs and ensure implementation of the requisite controls.
-
The consequences of negligence and non-compliance with state laws and policies may include department and personal:
-
Loss of delegated authorities.
-
Negative audit findings.
-
Monetary penalties.
-
Legal actions.
-
-
-
Auditing
-
The department has the right to audit any activities related to the use of state information assets.
-
CDT OIS and the department have the statutory right to audit department readiness to respond and recover from an incident.
-
-
Reporting
-
Violations of this policy shall be reported to the department ISO.
-
-
Security Variance Process
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request a security variance as defined by the ISO.
-
-
Authority
-
This policy complies with State of California Government Code Section 11549.3.
-
-
Revisions
-
The CIO or designee shall ensure that the contents of this article are current and accurate.
-
-
References
-
Statewide Information Management Manual 5305-A, Information Security Program Management Standard
-
Statewide Information Management Manual 120, Software Management Plan Guidelines
-
State Administrative Manual, Section 5305.5, Information Asset Management
-
State Administrative Manual, Section 5315.7, Software Usage Restrictions
-
State Administrative Manual, Section 4846.1, Software Management Plan
-
State Administrative Manual, Section 4846.2, Software Management Policy Reporting Requirements
-
National Institute of Standards and Technology, Special Publications 800-53, Configuration Management, CM-8, CM-10, CM-11
-
National Institute of Standards and Technology, Special Publications 800-53, System and Information Integrity, SI-7
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 3, Article 22
-
California Department of Corrections and Rehabilitation, Department Operations Manual Chapter 4, Article 45, Section 46030.4
-
California Government Code Section 11549.3
-
-
Revision History
-
Effective: 11/30/2022
-
5.3.27 Generative Artificial Intelligence
-
Policy
-
California Correctional Health Care Services (CCHCS) shall maintain requirements for all CCHCS workforce members on the appropriate use of Generative Artificial Intelligence (Gen AI) in its operations including, but not limited to, content creation, data analysis, and decision-making. CCHCS values information security and is committed to providing the necessary resources and training to support a secure environment.
-
-
Purpose
-
This policy defines the roles and processes for using Gen AI and applies to all information assets owned or operated by CCHCS or third parties on behalf of CCHCS.
-
-
Responsibility
-
The Chief Information Officer (CIO), CCHCS, shall act as primary executive sponsor for this policy.
-
-
Governance Roles
-
The CIO shall:
-
Determine risk response for all Gen AI uses and purchases, whether intentional or unintentional and shall not delegate the determination.
-
Ensure that all users of information assets are aware of this policy and acknowledge their individual responsibilities.
-
Review this policy annually and update as necessary to remain compliant with National Institute of Standards and Technology (NIST) PL-1 and California state regulations.
-
-
The Information Security Officer (ISO) shall:
-
Participate in risk assessments associated with Gen AI and related technologies.
-
Ensure that all use of Gen AI and related technologies are governed and approved prior to implementation.
-
Audit and assess compliance with this policy at least once every two years.
-
-
Information asset owners and program management shall ensure:
-
Personnel using Gen AI are trained for use according to their roles and responsibilities.
-
Risks associated with the use of Gen AI are identified, managed, monitored, and captured in the appropriate risk registry.
-
Gen AI applications are documented and inventoried.
-
All Gen AI usage has a qualified human reviewer as the ultimate decision maker for any process, input, or output that would directly impact a human.
-
A non-Artificial Intelligent (AI) alternative process is available if there are identified risks to humans, services, or systems.
-
-
Information Asset Custodians shall:
-
Implement, maintain, and monitor Gen AI access and security controls.
-
Collaborate with information asset owners and program management as necessary.
-
-
Information Asset Users shall be aware of and adhere to all information security and privacy policies.
-
-
Coordination Among Business Units
-
Information security policy development, review, and authorization shall be facilitated by the Regulation and Policy Section who is responsible for ensuring interdisciplinary participation from all business units.
-
This interdisciplinary engagement ensures policy alignment with operational reality, clinical needs, security and privacy obligations coupled with federal and state mandates.
-
-
Compliance
-
CCHCS workforce members shall adhere to all CCHCS Information Security policies and procedures.
-
Non-compliance with this policy may result in corrective or disciplinary action, up to and including termination as set forth in California Department of Corrections and Rehabilitation Department Operations Manual, Chapter 3, Article 22 and Title 15 Chapter 1.
-
If compliance is not feasible, or if deviation from this policy is necessary to support a business function, the respective manager shall formally request an exemption as defined by the Chief information Security Officer.
-
-
Directives for AI Usage
-
CCHCS shall ensure:
-
Gen AI procurements shall complete all processes and assessments for Gen AI as outlined in the Statewide Information Management Manual and the State Administrative Manual.
-
Gen AI and related technologies are approved and governed prior to use for official business purposes to ensure compliance with applicable industry standards, regulations, and laws.
-
Governance shall be conducted by a committee of relevant business stakeholders and technical experts from CCHCS as determined by the CIO and ISO.
-
-
The CIO and ISO shall document and inventory all Gen AI applications. The inventory shall contain a System Security Plan, which includes, but is not limited to:
-
System documentation.
-
Incident response plans.
-
Data dictionaries, if applicable.
-
Links to implementation software or source code.
-
Names and contact information for relevant AI actors.
-
-
CCHCS workforce members using Gen AI with data and information assets are trained regarding Gen AI use according to their roles and responsibilities.
-
Use of Gen AI in clinical settings, such as diagnostic support, care documentation, or summarization, include clinical validation and oversight by a licensed health care staff.
-
Gen AI tools shall not be integrated with Electronic Health Record Systems or clinical decision systems without explicit risk assessment and approval by the CIO and an equivalent Chief Medical Officer, if applicable.
-
Gen AI tools do not process or store Protected Health Information (PHI) or Personally Identifiable Information (PII) unless explicitly reviewed and approved by the Privacy Office and the CIO.
-
Use of Gen AI for data analysis in connection with any research project is prohibited unless the specific Gen AI model complies with all applicable federal and state laws and regulations, including but not limited to the HIPAA, the Common Rule (45 Code of Federal Regulations [CFR] Part 46), and state privacy and information security laws. If a Gen AI model is used with a research project the following shall occur:
-
De-identified of PHI and PII in accordance with 45 CFR 164.514.
-
Undergo an expert review and receive determination that the risk of re-identification is minor.
-
Incorporate safeguards to prevent bias and promote equity as outlined in California Government Code 11549.63.
-
Be approved by or receive a letter of exemption from an Institutional Review Board where required.
-
-
Gen AI and related technologies shall utilize the NIST 800-53 Revision 5 family of security controls at the moderate baseline.
-
Gen AI usage shall have a qualified human reviewer for any process, input, and output that could potentially yield unwanted impact to:
-
A person’s civil liberties, rights, physical or psychological safety, or economic opportunity.
-
A group such as discrimination against a population sub-group.
-
Democratic participation or educational access.
-
The business operations, reputation, information security or finances of an organization.
-
Interconnected and interdependent information assets.
-
The global financial system, supply chain, or interrelated systems.
-
Natural resources, the environment, or planet.
-
A human.
-
-
Gen AI usage shall have a non-AI process available if it could potentially harm the items listed in subsection (J).
-
-
-
References
-
Code of Federal Regulations, Health Insurance Portability Accountability Act, Summary of HIPAA Privacy Rule (45 CFR Parts 160, 164 Subparts A, C, and E)
-
Code of Federal Regulations, Health Insurance Portability Accountability Act, Security Rule (45 CFR 164 Subpart C)
-
Executive Order 14110 (Oct 2023) – “Safe, Secure, and Trustworthy Development and Use of Artificial Intelligence”
-
Executive Order N-12-23
-
California Civil Code, Division 1, Part 2.6, Section 56-56.16, et seq., Confidential Medical Information Act
-
California Civil Code, Division 3, Part 4, Section 1798.100, et seq., California Consumer Privacy Act & CPRA & 2023 Update
-
State Administrative Manual, Section 4986, Artificial Intelligence Introduction
-
State Administrative Manual, Section 4986.3, Gen AI Use Identification and High-Risk Inventory
-
State Administrative Manual, Section 4986.9, Gen AI Procurement
-
State Administrative Manual, Section 4986.10, Privacy for Gen AI
-
State Administrative Manual, Section 4986.11, Security for Gen AI
-
State Administrative Manual, Section 4986.12, Acceptable Use of Gen AI
-
State Administrative Manual, Section 4986.13, Gen AI Workforce Training
-
State Administrative Manual, Section 5305.5, Information Asset Management
-
State Administrative Manual, Section 5310.4, Individual Access to Personal Information
-
State Administrative Manual, Section 5310.6, Data Retention and Destruction
-
Statewide Health Information Policy Manual Section 3.3.5: Access Control
-
Statewide Information Management Manual, 5305-F, Generative Artificial Intelligence Risk Assessment
-
Statewide Information Management Manual, 5310-C, Privacy Threshold Assessment and Privacy Impact Assessments
-
Statewide Information Management Manual, 180 – Statement of Work Guidelines
-
Statewide Information Management Manual, 71A – Certification of Compliance with IT Policies Preparation Instructions
-
Statewide Information Management Manual, 71B – Certification of Compliance with IT Policies Template
-
Health Care Department Operations Manual, Chapter 5, Article 3, Section 5.3.15, Acceptable Use
-
Health Care Department Operations Manual, Chapter 5, Article 3, Section 5.3.19, Audit and Accountability
-
Health Care Department Operations Manual, Chapter 5, Article 3, Section 5.3.21, Data Security
-
-
Revision History
-
Effective: 03/18/2026
-
